The following article describes how to encrypt elastic block store (EBS) volumes on an intrusion detection system (IDS) appliance in the AWS EC2 console.
Solution
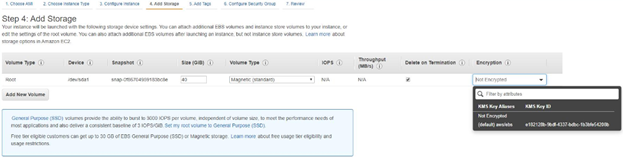
The following two options are available when encrypting EBS volume in the AWS EC2 console:
A. Create a new IDS with the EBS volume encrypted at the time of creation. This is done in step Add Storage.
B. Snapshot the existing EBS volume used by the IDS.
- Under Elastic Block Store, click on Volumes, and select the volume tied to the IDS instance.
- Click on Actions and choose Create Snapshot. The snapshot will show up under the Snapshots menu.
- Select the created snapshot, then click on the Actions button and choose Create Volume. Select the same Volume Type and Availability Zone as the existing IDS instance.
- Check the box to Encrypt this volume and set the Master Key. Choose (default) aws/ebs if no other key is available.
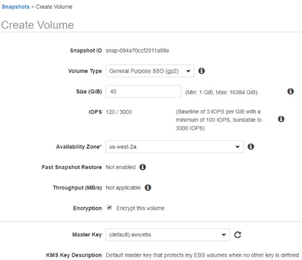
- Click on Create Volume. To detach the old volume and attach the encrypted one, the IDS must be stopped.
- On the Instances page, select the IDS instance, click on the Actions button and choose Instance State - Stop.
- On the Volumes page, select the unencrypted volume associated with your IDS instance, then click on the Actions button and choose Detach Volume.
- Select the new encrypted volume, click on the Actions button, then select Attach Volume.
- In the Attach Volume window, select the IDS instance (stopped), change the device to /dev/sda1 (to attach it as the root volume), then click on the Attach button.
- Start the IDS instance.
Comments
0 comments
Please sign in to leave a comment.