The Joomla CMS core product code is vulnerable to a SQL injection attack. This enables an attacker to directly send code to the backend SQL server to be executed. This may result in data exfiltration or data being deleted.
Exploitation
Stages
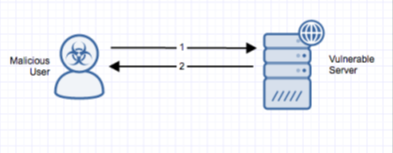
- A remote unauthenticated attacker makes a request to the server running a vulnerable version of Joomla, with a boolean-based blind or error-based SQL injection in the list[fullordering]=parameter.
- The server responds with a 500 internal server error, and the attacker retrieves information about the database.
Prerequisites
No prior authentication is needed to create a successful exploit
Vulnerability Description
There is a vulnerability in version 3.7 of the Joomla CMS. It is caused by a component named ‘com_fields’. To exploit this vulnerability, all an attacker must do is add the proper parameters to the URL to inject nested SQL queries into the parameter ‘list[fullordering]=’. The result of this attack could include leaking password hashes and hijacking a logged-in user’s session (the latter results in a full site compromise if an administrator session is stolen).
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
In addition, detection of this threat is provided via the AlertLogic ActiveWatch™ for Web Security Manager™ service. Depending on your deployment of Web Security Manager, you will receive an incident (for out-of-band deployment) or the threat will be actively blocked and rejected (for the inline Web Security Manager Premier deployment) if an exploit attempt is observed.
Recommendations for Mitigation
Check web server access logs for requests to the vulnerable page with a SQL injection in the parameter This will only be effective if the attack is carried out in the URI.
Upgrade to Joomla 3.7.1 to mitigate the vulnerability.
Comments
0 comments
Please sign in to leave a comment.