Nishang is a framework and collection of scripts and payloads which enables the usage of Powershell for offensive security, penetration testing, and red teaming. An attacker can utilize the framework via gaining a foothold on a Windows server and installing/calling functions from the framework.
Exploitation
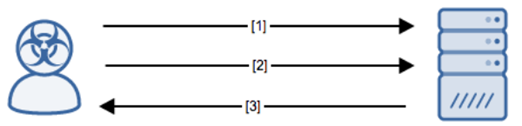
Stages
- The attacker exploits a Windows server via an unknown mechanism.
- The attacker installs/calls functions from the Nishang framework to act upon their objectives.
- The server returns the information/response that the attacker wants.
Prerequisites
The attacker will need some level of access to the server either via an exploit or stolen credentials.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
Detection of this threat is provided via the Alert Logic ActiveWatch for Log Manager™ service. Log messages are produced by the vulnerable system when an exploit of this type is leveraged. An incident will be generated in the Alert Logic console if these log messages are observed.
Recommendations for Mitigation
The attacker must have exploited some other entry vector to gain access to the local victim host. Ensure that all software on internet-facing hosts is up-to-date.
Comments
0 comments
Please sign in to leave a comment.