BTCWare is a standard server-side ransomware malware. It encrypts data on the victim machine and demands payment for return of the encrypted data.
Exploitation
Stages
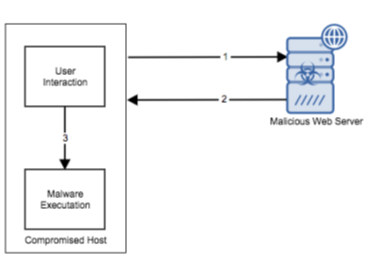
- The victim or malicious user requests the server-side ransomware from the malicious webserver.
- The software is delivered to the compromised host.
- The server-side ransomware is manually detonated on the compromised host.
Prerequisites
No prior authentication is needed to create a successful exploit
Vulnerability Description
BTCWare is server-side ransomware that is used to take a victim’s files hostage and then demand payment in exchange for a code that returns access of the seized files back to the victim. The BTCWare server-side ransomware is just one of many server-side ransomware attacks that is being used to extort money from victims.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
Detection of this threat is provided via the Alert Logic ActiveWatch™ for Log Manager™ service. Log messages are produced by the vulnerable system when an exploit of this type is leveraged. An incident will be generated in the Alert Logic console if these log messages are observed.
Recommendations for Mitigation
To confirm a BTCWare infection, a user may observe multiple files with the extension of “.onyon”, “.btcware”, “.blocking”, “.xfile”, “.master”, “.theva”, “.cryptobyte”, or “.cryptowin” on the file system. The extension depends on the version of the server-side ransomware. BTCWare also creates a ransom note HTM file (‘#_HOW_TO_FIX_!.hta.htm”), “!#_RESTORE_FILES_#!.inf” or “!#_DECRYPT_#!” and places it on the desktop. This note is also dependent of the variant that performed the infection.
BTCWare is a server-side ransomware that is used to take a victim’s files hostage and then demand payment in exchange for a code that returns access to the seized files back to the victim. Performing the payment only encourages more of this type of activity. The best method to remediate this issue is to reformat and reinstall the host from the last known good backup. In addition, a tool is available that may decrypt files infected by one of more the BTC server-side ransomware varients. This tool is located here: http://malwarewarrior.com/remove-btc-ransomware-decrypt-btc-files/#decrypt
Comments
0 comments
Please sign in to leave a comment.