The 'All in One WP Security & Firewall' WordPress Plugin keeps a log of security events to be reviewed by an administrative user. In versions below and including v.4.2.5, these log files are publicly accessible without authentication, allowing any unauthenticated user to successfully request the known file path to these security logs.
Exploitation
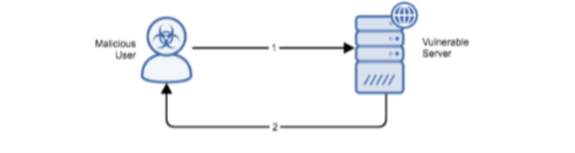
Stages
- User sends HTTP GET request to vulnerable log file.
- WordPress application responds with contents of the requested file.
Prerequisites
This vulnerability exists on installations of the “All in One WP Security & Firewall” plugin for WordPress including and previous to v.4.2.5.
Vulnerability Description
This plugin generates security logs to be reviewed by the applications administrative user. However, insufficient privilege and authentication checks are carried out when a user directly requests the logs generated by the plugin, allowing any user to retrieve these logs. These logs store security notifications for the administrators of WordPress web applications, noting any security events or suspicious activity.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Upon discovery of a successful exploit, customers are expected to take normal and reasonable action in accordance with their own standard operating procedures, such as:
- Isolate vulnerable device from network
- Block access to the vulnerable log files using .htaccess or httpd.conf or firewall
- Try to identify an alternative plugin serving similar functionality until an appropriate patch is available
- Test the device
- Return the compromised device to the network and full operation
Comments
0 comments
Please sign in to leave a comment.