There is a buffer overflow vulnerability in the Linux pmmasterd daemon when handling requests of type ACT_ALERT_EVENT. Successful exploit could lead to the attacker compromising the server.
Exploitation
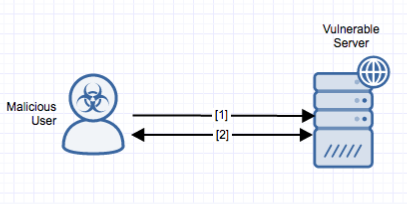
Stages
- A remote unauthenticated attacker sends a crafted request to the policy server. The buffer overflow is triggered when handling requests of type ACT_ALERT_EVENT.
- The attacker transfers a shell onto the vulnerable server allowing them to execute arbitrary code on the system.
Prerequisites
The server is only vulnerable when configured as a policy server.
Vulnerability Description
There is a buffer overflow vulnerability in Quest Privilege Manager. The vulnerability exists in the pmmasterd daemon and can only be triggered when the host has been configured as a policy server. A buffer overflow condition exists when handling requests of type ACT_ALERT_EVENT, where the size of memcpy can be controlled by the attacker. Successful exploit could lead to the attacker compromising the server.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Deploy the latest vendor updates. Issues have been fixed in version 6.0.0-61.
Comments
0 comments
Please sign in to leave a comment.