The WordPress Plugin MM Forms Community is prone to a vulnerability that lets attackers upload arbitrary files. An unauthenticated attacker can exploit this vulnerability to upload arbitrary PHP code and run it in the context of the web server process. This can lead to arbitrary code execution on the server and complete compromise of the target server.
Exploitation
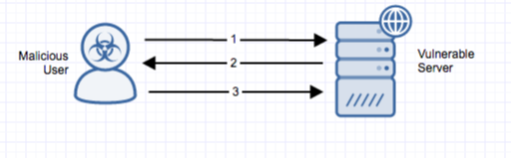
Stages
- The remote unauthenticated attacker sends a request to ‘mm-forms-community/includes/doajaxfileupload.php;’ and uploads a malicious file.
- The server responds successfully, noting that the file has been uploaded.
- The attacker requests their uploaded file at ‘mm-forms-community/upload/temp/’.
Prerequisites
The vulnerable plugin must be installed on the target system.
Vulnerability Description
The WordPress Plugin MM Forms Community is subject to a vulnerability that lets attackers upload arbitrary files. The issue occurs because the application fails to adequately sanitize user-supplied input. An unauthenticated attacker can exploit this vulnerability to upload arbitrary PHP code and run it in the context of the web server process. This can lead to arbitrary code execution on the server and complete compromise of the target server.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
To mitigate the vulnerability, restrict access to the vulnerable file via .htaccess.
Comments
0 comments
Please sign in to leave a comment.