A script injection vulnerability has been found in Apache Struts 2. A remote, unauthenticated attacker can exploit this vulnerability by sending a crafted HTTP request to a vulnerable Struts 2 web application. A successful attack will result in the execution of OS commands in the security context of the web application server.
Exploitation
Stages
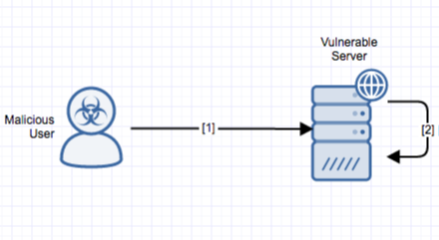
- A remote, unauthenticated attacker sends a crafted HTTP request. The request contains a crafted URI/client body parameter value with an OGNL expression.
- The vulnerability is triggered when the affected ConversionErrorInterceptor processes the type conversion error, executing the OGNL statement.
Prerequisites
The attacker must have access to the vulnerable system using arbitrarily crafted packets.
Vulnerability Description
A script injection vulnerability has been found in Apache Struts 2. The vulnerability is due to a design error; HTTP request parameters are interpreted as OGNL expressions when conversion errors occur.
A remote, unauthenticated attacker can exploit this vulnerability by sending a crafted HTTP request to a vulnerable Struts 2 web application. A successful attack will result in the execution of arbitrary OGNL expressions (possibly OS commands) in the security context of the web application server.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Detection of this threat is provided via Alert Logic ActiveWatch for Web Security Manager™ service. Depending on your deployment of Web Security Manager, you will receive an incident (for out-of-band deployment) or the threat will be actively blocked and rejected (for the inline Web Security Manager Premier deployment) if an exploit attempt is observed.
Recommendations for Mitigation
Update to latest version of Apache Struts.
Comments
0 comments
Please sign in to leave a comment.