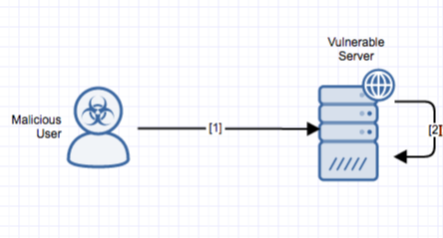
A command execution vulnerability exists in Apache's Struts 2 framework. A remote attacker can craft an HTTP request to cause a target server to execute arbitrary code.
Exploitation
Stages
- A remote unauthenticated attacker connects to the target Struts 2 framework-based application and sends a crafted HTTP request. The request contains a malicious OGNL expression.
- The vulnerability is triggered when the affected module evaluates the value as an OGNL expression.
Prerequisites
The attacker must be able to send arbitrary packets to the victim host.
Vulnerability Description
A command execution vulnerability exists in Apache's Struts 2 framework. The vulnerability is due to a lack of sanitization inside the Java class ParametersInterceptor that improperly allows parentheses in HTTP parameters. A remote attacker can craft an HTTP request to cause a target server to evaluate an arbitrary OGNL expression and consequently execute arbitrary code. Note that none of our current coverage covers this vulnerability.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Update to a non-vulnerable version of Apache Struts to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.