There is a vulnerability in the Java JMX server. The vulnerability is due to an insecure deployment, allowing a user to connect to and interact with the service. This can lead to total compromise of the victim server.
Exploitation
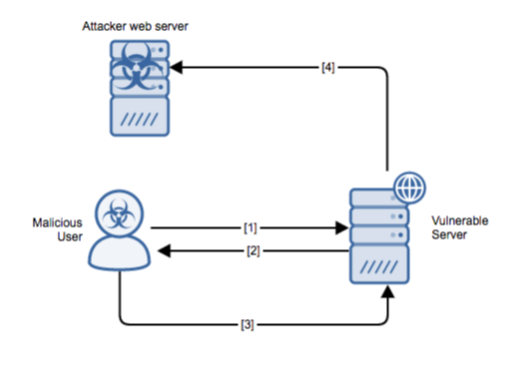
Stages
- The attacker sends an RMI header.
- The server responds with the JMXRMI endpoint.
- The attacker proceeds with the handshake with the JMX Bean Server, accessing the vulnerable function ‘javax.management.loading.MLet’.
- The JMX agent on the victim server accesses the remote URL that is hosting the malicious JAR file on the attacker web server. When the JMX service registers the MLet file, the agent will initiate the URL to the remote JAR and execute the methods leading to code execution.
Prerequisites
The attacker must have direct access to the vulnerable victim host.
Vulnerability Description
There is a vulnerability in the Java JMX server. The JMX service allows users to call the ‘javax.management.loading.MLet’ function, which permits the loading of an MBean from a remote URL. An attacker can set up their remote web server to host an MLet (text file) that points to a malicious JAR file. When the JMX service registers the MLet file, the agent will initiate the URL to the remote JAR and execute the methods leading to code execution. This can lead to total compromise of the victim server.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Update the software to a non-vulnerable version.
Comments
0 comments
Please sign in to leave a comment.