The IndoXploit shell suite of tools is used to compromise content management systems (CMS) running LAMP stacks.
Exploitation
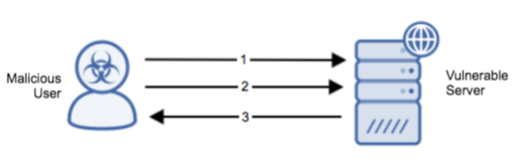
Stages
- The malicious user exploits an attack vector such as outdated software or a misconfigured server to install the web shell.
- The malicious user interacts with the web shell and allows the attacker to use web shell functions on the compromised webserver.
- A status is returned from the web shell indicating that its usage has been successful.
Prerequisites
An exploitable file upload vulnerability must be resident on the target system.
Vulnerability Description
The IndoXploit shell suite of tools is used to compromise CMSs running LAMP stacks. Some features of this toolset consists of OS commanding, mass defacement, searching for configuration files, jumping to different user accounts, cracking cPanel passwords, and grabbing SMTP logins.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
To mitigate the potential for web shell infection, ensure that all software and systems have applied the most recent security updates.
Comments
0 comments
Please sign in to leave a comment.