In versions of Joomla < 3.8.0, inadequate escaping in the LDAP authentication plugin can result in a disclosure of usernames and passwords. A successful attack may allow remote access to malicious users in the context of the compromised user’s credentials.
Exploitation
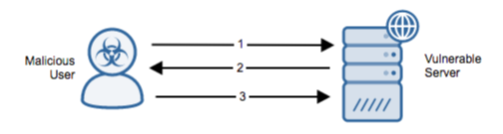
Stages
- The malicious user sends a malicious LDAP query to Joomla’s authentication page for the LDAP plugin to execute.
- Information is returned to the attacker indicating if the search was successful.
- This process is repeated until the valid username and credentials are leaked.
Prerequisites
The attacker must have access to the admin URL. The system must be configured to use LDAP authentication as the only form of user authentication.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
To mitigate the vulnerability, upgrade to a non-vulnerable version of the plugin.
Comments
0 comments
Please sign in to leave a comment.