A remote code execution (RCE) vulnerability exists in the ajax_create_folder.php script used in the Ajax File and Image Manager software package. This vulnerability is present in version 1.0. An attacker is able to inject PHP payloads via crafted requests, resulting in the ability to run arbitrary commands on the target host. No authentication is required for successful exploitation of this vulnerability.
Exploitation
Stages
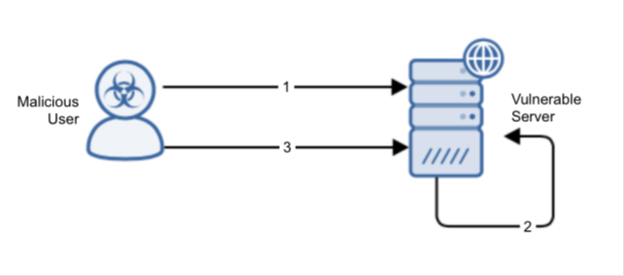
- The attacker sends an HTTP POST request to ajax_create_folder.php with a malicious PHP payload contained in the POST body.
- The injected payload buffer is passed to a writeInfo function within inc/function.base.php which is then written to inc/data.php.
- The attacker makes a request to/inc/data.php. The output of the injected PHP code is returned.
Prerequisites
The attacker must be able to send crafted packets to the ajax_create_folder.php script hosted on the target webserver.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Detection of this threat is provided via Alert Logic ActiveWatch for Web Security Manager service. Depending on your deployment of Web Security Manager, you will receive an incident (for out-of-band deployment) or the threat will be actively blocked and rejected (for the inline Web Security Manager Premier deployment) if an exploit attempt is observed.
Recommendations for Mitigation
To mitigate the vulnerability, upgrade to a non-vulnerable version of the software.
Comments
0 comments
Please sign in to leave a comment.