Threat Summary
Overview
Version 3.31.17 and lower of the WordPress plugin VideoWhisper Video Presentation and version 4.91.8 and lower of VideoWhisper Video Conference Integration allow the unauthenticated upload of executable PHP code.
Exploitation
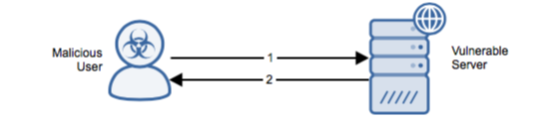
Stages
- The attacker sends an HTTP POST with executable code contained in a phtml/shtml file to the vulnerable plugin.
- The server responds with HTTP 200 OK and “loadstatus=1”.
Prerequisites
The attacker can access vulnerable PHP code directly and without authentication.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.