CakePHP versions 1.3.X to 1.3.5 and 1.2.8 are vulnerable to a PHP object injection. Serialized data appended to CSRF security tokens are passed unchecked to PHP unserialize. An attacker can provide a serialized app object that will corrupt the Cake cache, leading to the execution of arbitrary local files. Attackers can embed PHP code within the corrupted cache to gain remote code execution (RCE).
Exploitation
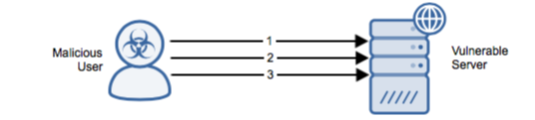
Stages
- The attacker sends an HTTP GET/POST request to the application. The legitimate app object flushes to the cache.
- The attacker sends a crafted HTTP POST request with PHP code embedded within a serialized malicious app object that has been appended to the CSRF token. The destructor function of the malicious app object will corrupt the Cake cache by inserting a path to itself and the PHP payload.
- The attacker sends an HTTP GET request. The legitimate app object will read the corrupted cache and then include the cache file itself, executing the PHP code and providing the attacker with RCE.
Prerequisites
The target must have POST forms with CSRF security tokens enabled.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.