Plupload is a file upload library that provides polyfills—JavaScript that emulates HTML5 functionality—for the XMLHttpRequest, file, and image APIs. The library comes with the examples sub-directory, containing upload.php, which is potentially vulnerable to arbitrary file upload.
Exploitation
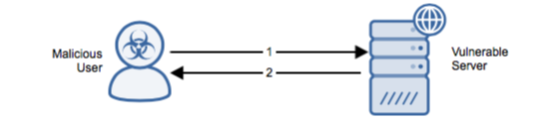
Stages
- The attacker sends an HTTP POST with executable PHP file to plupload/examples/upload.php.
- The server replies with an HTTP 200 OK and JSON message. It is unknown whether the upload was successful despite the absence of an error message.
Prerequisites
- The attacker can access and execute upload.php directly and without authentication.
- The PHP configuration variable upload_tmp_dir must have been set by the admin.
- php has been modified to allow upload even if upload_tmp_dir was not set.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.