The latest version and older (<= 1.1) of the Simple Photo Gallery Joomla component is vulnerable to arbitrary file upload by unauthenticated attackers. Any file can be uploaded due to the code not making use of the variable that was set to indicate that the extension is invalid.
Exploitation
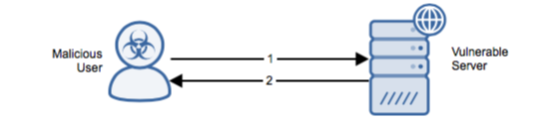
Stages
- The attacker sends HTTP POST with executable PHP file to vulnerable Simple Photo Gallery component.
- The server replies with HTTP 200 OK and the name of the uploaded file.
Prerequisites
The attacker can access the vulnerable upload functionality directly and without authentication.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.