Computing environments are extremely important corporate tools that let companies work efficiently and effectively within the technology-enabled global economy. As technology continues to evolve and become more complex, it also becomes more difficult to secure. As a result, online retailers and healthcare providers continue to experience data breaches. Victims of data compromise are often certified as Payment Card Industry (PCI) or Health Insurance Privacy and Acceptability Act (HIPAA) compliant but are found to lack sustainable processes and procedures after close investigation.
Alert Logic® enables organizations to offer managed security and compliance services with our patented, cloud-enabled technology platform. Most application components are hosted in Alert Logic's data center. They process data in real time through our security systems architecture. Alert Logic and service provider customers can manage log data, detect and respond to threats, and proactively manage vulnerabilities. Many organizations leverage Alert Logic as a cornerstone of their security and compliance architecture.
When our customers and partners entrust their security to Alert Logic, they can have confidence that we take the task seriously. We protect our customer data with a risk-based, in-depth approach to security. Our security strategy combines information security policies and best practices with patented, state-of-the-art technology to deliver deep security insight and continuous protection of our customers' most sensitive data.
Alert Logic adheres to three essential security principles: confidentiality, integrity, and availability. Our employees maintain the highest ethical standards of professional conduct. With Alert Logic, you can rest assured that your sensitive intellectual property is secure.
In This Article
- Information Security & Compliance
- Personnel Security
- Physical & Environmental Security
- Logical Access Controls
- Technical Controls
- Backup & Recovery
- Customer Data
- Customer Information Privacy
Information Security & Compliance
Alert Logic has established an information security and compliance program that is based on ISO/IEC 27001:2013 information security standards. The program is designed to protect our information resources and to enable compliance with applicable regulatory requirements. It establishes internal controls through the definition of security policies, standards, guidelines, and procedures. Our internal control environment ensures the confidentiality, integrity, and availability of Alert Logic's infrastructure and resources.
As a security and compliance service provider, Alert Logic engages third-party independent auditors to perform an annual Statement on Standards for Attestation Engagements No. 18 (SSAE 18) Type II audit of our internal controls, an annual Payment Card Industry Data Security Standard (PCI DSS) Service Provider compliance review, and an annual ISO 27001:2013 compliance review. In the case of the SSAE 18 audit, the service auditor's opinion attests to the fact that the controls related to the specified audit period to achieve those control objectives.
The results of the audit period under review are available to you in the Compliance category of our Support Center after logging in with your product credentials. If you do not have product credentials, simply contact your Alert Logic sales representative or submit a request ticket through Customer Service.
Personnel Security
Alert Logic employees are required to meet a minimum level of education and experience commensurate with each role within our company. Our Talent Management department conducts background checks on all employees and contractors, which include:
- State and local criminal history
- National criminal history
- Personal, professional, and education reference verification.
New employees are required to sign a Confidentiality Agreement and an Acceptable Use Policy. The Acceptable Use Policy is a compliance statement that acknowledges the employee's willingness to comply with and their understanding of acceptable IT usage and Information Security policies. Additionally, employees are required to provide formal acknowledgment of Alert Logic Corporate Policies on an annual basis.
All employees are also required to complete security and compliance related training modules within two weeks of initial employment. These include:
- Security Awareness Training
- Global Privacy & Information Security
- Business Ethics
- Foreign Corrupt Practices Training.
Alert Logic employees adhere to specific password requirements, and passwords expire and must be regenerated every 90 days. Employee passwords must:
- Contain at least 10 characters
- Contain at least one upper-case and one lower-case letter
- Contain at least one number
- Contain at least one special character
- Cannot be identical to the current or previous four passwords
- Account lockout after five incorrect password attempts
Alert Logic enforces the segregation of duties by restricting physical and logical access to authorized personnel only. All corporate systems are operated under the principal of least privilege, meaning that they run with the least amount of privilege necessary to perform specific functions. Employee access to these systems is granted on a need-to-know basis.
Physical & Environmental Security
The Alert Logic global headquarters is located in Houston, TX, and our European corporate headquarters is located in Cardiff, Wales. We have satellite offices in: Dallas, TX; Austin, TX; Seattle, WA; London, UK; Belfast, UK; Cali, Colombia.
Alert Logic utilizes three primary co-location data centers to host our production environments and three secondary redundant disaster recovery co-location data centers.
Corporate Offices
Alert Logic's corporate offices include all departments necessary to sustain our business. These include, but are not limited to, our Operations, Research & Development, Security Operations, and Support functions. All offices are equipped with digital closed-circuit television surveillance systems to monitor access to Alert Logic facilities and Security Operations Centers. Surveillance cameras are located at various ingress and egress points and are monitored 24x7x365.
Visitors to our corporate offices are required to wear visitor badges and are escorted by employees at all times while within our facilities. Employees and contractors are required to use a combination of card keys and numeric keypad readers to enter offices. These security mechanisms control access to buildings during business and non-business hours and restrict resources to appropriate personnel.
Data Centers
Our data centers are in highly secure co-location facilities. These facilities are protected with various physical and environmental access controls that would be difficult and costly to duplicate in our corporate offices.
The buildings that house our data centers are reinforced physical structures that feature access control mechanisms such as:
- Concrete bollards around perimeters
- Steel-lined walls
- Bulletproof glass
- Barbed wire perimeters.
The facilities are protected by onsite security officers and state-of-the-art recording systems 24x7x365.
Fire protection systems include smoke detectors and suppression systems designed to provide early warning and containment of a fire. Air conditioning is used to control temperature and humidity to acceptable operating ranges. Raised floors and seismically rated equipment protect against water, hurricane, and earthquake damage. The facilities include diesel-powered electrical generators, back-up battery systems, and redundant external communication connections.
Logical Access Controls
Alert Logic employees are explicitly granted only the rights, privileges, and access necessary to accomplish their assigned duties. Development, back office, and production systems are managed by separate IT groups.
Access to all systems requires management approval, a user ID, and a password. Users and administrators are uniquely assigned user IDs in order to be identified and authenticated to our systems. User IDs provide the mechanism by which we promote resource availability and protect our systems from unauthorized access, alteration, loss, and disclosure of information.
Local and remote authentication to productive environment systems are protected by VPN and multi-factor authentication with standard password controls. All employees are responsible for maintaining the confidentiality of their passwords.
Pending an employee termination, either Talent Management or the employee's manager provides advanced notification to IT and Infrastructure. Once employment has been terminated, the former employee's accounts are immediately deactivated. Alert Logic performs periodic reconciliations in order to ensure that only current employees are active in our systems. Inactive user accounts are disabled or removed as necessary.
Each customer's data is stored in either a private table space or private database, and these private spaces are never shared across customers. In addition, customer-specific data is stored in a namespace associated with that particular customer. All application users must first authenticate as a user in that namespace to gain access to the data.
When an application user accesses the Alert Logic console for the first time, they are required to change their password upon initial login.
Technical Controls
Appliance Security
Alert Logic product and service deployments include one or more appliances installed in a service provider or customer environment. The appliances are based upon a purpose-built hardened Linux operating system. Firewall software reduces each appliance's application footprint and threat vector. Every individual appliance is created with unique passwords, and no default logins are present on any appliance. All appliance configuration data is stored on the appliance and mirrored in the data center facility for easy recovery in the event of appliance failure.
To reduce risk of inadequate security configurations on Alert Logic appliances, the appliance base image is created from Linux minimal install with the additional of SSHD, Apache, Open SSL, and the Alert Logic appliance software. This approach eliminates the need to remove or disable unnecessary services, daemons, scripts, ports, protocols, functions, accounts, etc. for the appliance prior to implementation. Additionally, two user accounts are created and the credentials are provided to the customer for limited setup and configuration of the appliance. A special support user account with limited permissions is available for support personnel to provide technical support of the appliance, when necessary.
Alert Logic utilizes a firewall on each appliance to ensure that access is securely guarded and managed. As part of this configuration, the firewall rules are stringently configured to only allow RFC1918 and Alert Logic's own IP ranges. This eliminates exposure to the greater Internet. The appliance will allow SSH connections, but only from authorized users who are connecting from our IP ranges.
The appliances regularly communicate with the Alert Logic data center through encrypted Internet channels. The encryption technology utilized varies depending on the service. The network intrusion detection system (IDS) uses the Advanced Encryption Standards (AES) with 256-bit symmetric keys, while log management and web application IDS use Secure Sockets Layer (SSL) with 2,048 primes.
Note: The data in Alert Logic log management is not encrypted at rest. It is only cached locally, then it is encrypted and sent to our data center where it is then encrypted at rest using AES 256. Once the data is transported, it is cleared from the cache.
There are three scenarios related to appliance access:
1. Data "push" - the appliances communicate with our data center by sending on-demand data that enables our service. Network IDS appliances send threat data as events are triggered, and vulnerability data as scans are completed. Log management sends a continuous stream of log data. Web application IDS sends a stream of configuration data, statistics, and detailed blocking data on a regular frequency. Integrity checking is performed on network IDS and log management. Web application IDS data is transmitted from appliances and maintained on servers at the primary data center facility to verify availability, validity, and completeness. Transaction logging is also enabled on Alert Logic servers to facilitate transaction research and data accuracy verification. All appliances regularly send administrative data that enables their remote management and performance monitoring.
2. Data "pull" - the appliances communicate by pulling software and security content updates from the Alert Logic data center.
Network Intrusion Detection
Alert Logic's security research team drives the creation of new threat and vulnerability signatures designed to meet newly identified threats. Signatures are first tested on test sensors for detection accuracy, false positives, and flooding. Once the signatures are ready for rollout, they are placed in our signature repository for pickup. This rollout is phased and closely monitored. The appliances check and download signature updates every five to ten minutes. Once the signatures are on the appliance, they are moved to a temporary location and sensors install and test them. If an error is detected, the update is not applied and an error is reported. Errors are investigated, fixed, and the signatures redeployed. Signature updates sometimes occur on a daily, but at minimum, weekly, basis.
Web Application Intrusion Detection
Native security signatures are first tested on appliances for detection accuracy and false positives. Once the signatures are ready for rollout, they are placed on our updated server for pickup. The appliances check and download signature updates on a regular basis. Once the signatures are on an appliance, they are moved to a temporary location, where they can be applied upon approval by the customers.
3. Employee access to the remote appliances - Authorized Alert Logic staff members have controlled access to appliances for a variety of job-specific purposes, including appliance system administration, updates, content tuning, and general package management. Appliances only allow communication to Alert Logic-owned IP ranges that go to various backend services. In order for an authorized user to access an appliance, the primary method is for an appliance to initiate a reverse shell after receiving a message from the Alert Logic backend stating that a task is in need of execution. This causes the appliance to then initiate a secure SSL connection from the customer network over outbound port 443 to a jump server located at the Alert Logic backend. This jump server instance enables authorized users to then execute necessary tasks on the appliance. However, an inbound SSH connection to the customer environment is an option if the primary method is not available.
Data Security
Our IT staff closely evaluates all third-party software applications before implementation. Change control processes manage our software lifecycle through research and development, quality assurance, and into production. Software hot fixes are documented and approved by management.
All third-party software patches and upgrades are thoroughly vetted and tested before they are applied to production servers. Alert Logic Audit & Compliance and Corporate Security teams regularly conduct internal security audits and vulnerability testing against the production network and systems to identify and correct areas of potential exposure before application to servers. Resolving vulnerabilities in third-party applications goes as follows:
- Alert Logic Research monitors advisories for all third-party software applications that are running on appliances and internal systems.
- Any newly identified vulnerabilities are analyzed for impact and severity, and then analyzed against the compensating controls we have in place to protect appliances. These controls are primarily related to the firewall configuration on the host, but also relate to appliances only accepting connection attempts from Alert Logic IP spaces.
We log, monitor, and review our server and application event logs on a daily basis. Administrative users are required to log onto appliances and our servers as non-privileged users and then switch to privileged accounts. The act of switching is logged by our servers. We do not allow remote root logins to our systems.
Network Security
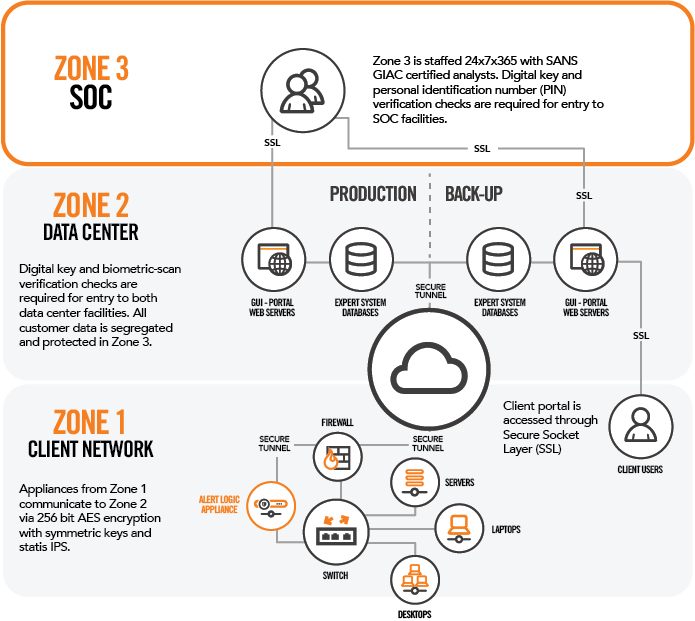
Alert Logic production firewalls establish a De-Militarized Zone (DMZ) to segregate customer data from our corporate and production networks. The system architecture is divided into several logical zones.
Zone 1
This zone is located on the service provider or customer's network and is comprised of the Alert Logic appliance.
Zone 2
Our data center facility is the next zone. The components of this zone include our load-balanced web servers, expert system, and external scanning appliance.
Our web servers, accessible via the Internet and through API end-points, handle access to our management portal. Transport between the client and our web servers is protected by SSL sessions. Our front-end systems provide access and technical controls such as input validation, designed to protect customer data.
During data processing, our patented expert system receives the encrypted data feed from Zone 1 via our receiver nodes. Besides our management user interface, the receivers and API end-points, accessible with API keys provided to customers by Alert Logic, are the only other publicly accessible pieces of our technology. They utilize proprietary protocols for inbound appliance communication. These are the only communication channels allowed between them and the web nodes.
Back end systems are protected by our firewalls and are not accessible from the Internet. All clients accessing data such as the user interface, expert system, etc. are tightly controlled and use standardized authentication and identification APIs that prevent unauthorized access to data. All log data are hashed using SHA256 and the hashes are stored in separate storage clouds from the packets themselves. The hashes are used to protect the integrity of log data.
The network architecture supporting these systems is designed for maximum security and reliability. The production network consists of multiple autonomous data bases, processing nodes, and storage instances that support different groups of customers.
The processing instances are internally load-balanced to evenly distribute processing and communications activity across network links and CPUs for optimal I/O performance and traffic throughput.
Subsystem redundancy within the clusters provides a high degree of fault tolerance to counteract unexpected hardware or software failures. If one computer system or component fails, a duplicate system or component automatically takes over. In addition, access to the Master Database containing customer transaction data is restricted by IP address. This architecture allows us to manage individual components with no impact to other components. Any variance from normal system behaviors, or any abnormal activity at all, can identify the need to quarantine or shut down those nodes.
An online record of transactional data is available for six months on the Alert Logic server. All files submitted to the Alert Logic Master Database are validated against the Alert Logic transactional data schema. Files that fail this process are rejected and no items within the file are accepted for exchange.
Zone 3
Our Security Operations Center comprises the third and final zone, and is staffed 24x7x365. This team of security analysts assists customers with the identification and escalation of network security incidents and vulnerabilities. The Security Operations team also performs log review duties during Alert Logic business hours.
Vulnerability Management
Alert Logic's Vulnerability Management Process is designed to take into consideration the vulnerability risk of the asset and impact to the business, and then to identify the urgency and required action associated. Alert Logic understands that mediating identified risks is extremely important; however, thoughtful consideration must be taken to ensure the service provided to customers is not negatively impacted as well. In order to ensure this is considered, an urgency matrix and a process workflow have been defined to ensure the proper urgency is set, communication is established with customers if necessary, and that impacted systems have as many vulnerabilities addressed at one time as possible.
Backup & Recovery
Alert Logic production data centers are a dual processing pair to provide disaster recovery and business continuity in the event of a catastrophic failure. The production network's instances are duplicated through leverage of real-time replication capabilities of our database technologies, data processing system, and the enterprise storage systems and are configured to mirror all operational data. Replication activities are monitored in real time by our 24x7x365 monitoring and alerting system. If there are system failures or reductions in performance, alert notifications are sent to the Infrastructure and Production Support groups.
Upon initial deployment, application configurations are centralized and stored in our data center environment. Changes to appliance configurations are captured and backed up via the replication process.
Customer Data
Alert Logic understands the sensitive nature of the data that is processed and stored on our systems. Our security policies and procedures are designed to protect your information from inadvertent disclosure. Each customer's data is stored in either a private table or private database, and these private spaces are never shared across customers. In addition, all customer-specific data is stored in a namespace associated with that customer and all application users must first authenticate as a user in that namespace to gain access to the data. Namespaces that are accessed are not directly specified by user input and are always assigned by low-level components only after verifying a specific user, customer, and password combination. This combination is verified on every individual data request.
As part of the life cycle management of our physical appliances, Alert Logic contracts with a third-party provider that specializes in performing secure sanitization of media in accordance with NIST SP 800-88. Once disposal has been completed by the vendor, a certification of data destruction is provided.
It is also important to note that Alert Logic is currently protecting 3,800+ customers, including those with compliance requirements such as the Gramm-Leach-Bliley Act (GLBA), the Health Insurance Portability and Accountability Act (HIPAA), and the Payment Card Industry Data Security Standard (PCI DSS).
Customer Information Privacy
Alert Logic respects the privacy of all customers and website visitors. We have established a Privacy Policy as a commitment to maintain the privacy of your personal information in connection with all of your online interactions with us.
Use of Personal Information
Personal information shared with Alert Logic by customers is securely protected. Alert Logic may gather information about customers through customer use of our website and services in various ways.
- We may collect and store some personally identifiable information, such as your first and last name, telephone numbers, physical addresses, and e-mail addresses. These are provided to Alert Logic by customers for the purposes of facilitating use of the Alert Logic website and services, handling correspondence with customers, and registering credentials for site access entitlements.
- We may collect and store information about your visits and interactions with our website in collective or aggregated data that does not identify you specifically, but is automatically received and recorded by us through the use of "cookies".
Cookies, also known as HTTP cookies, web cookies, or browser cookies, are used by our website to communicate state information to and from your browser and the website. The state information can be used for session identification, user preferences, or anything else that can be accomplished through storing text data associated with providing our services. Cookies cannot be programmed, cannot carry viruses, and cannot install malware on your computer.
We use site-related information to help maintain accurate accounts, to provide and to change services, to provide accurate billing and shipping, to answer your product and service inquiries, to market services and products, and to ensure that our website is useful to you. Alert Logic does not market to or collect personal information about children under 13 years of age via any website, product, or service.
Sharing Information
As a general rule, Alert Logic does not sell, trade, or disclose personal information gathered online about you to third parties without your consent. The only exceptions to this rule are:
- When we work with affiliated businesses, partners, or agents to develop a relationship with you or to perform services for you on our behalf. We require the relevant businesses, partners, or agents to adhere to our policies regarding the use and protection of your personal information.
- As may be required by subpoena, search warrant, or other legal process or in the case of imminent physical harm to your or others.
Access
If you'd like a copy of your personal information that Alert Logic collects or would like to correct, amend, or delete certain personal information collected by Alert Logic, you can contact us with your request via email at privacy@alertlogic.com.
Comments
1 comment
This is a complete and comprehensive staement! I would like to have each and every service provider to have a statement like this!
Please sign in to leave a comment.