CrypMIC is a forked variant of the CryptXXX server-side ransomware, which is distributed and functions identically to the last CryptXXX campaign. It also utilizes the same C2 functions, including static strings observed in unencrypted traffic over port 443.
Exploitation
Stages
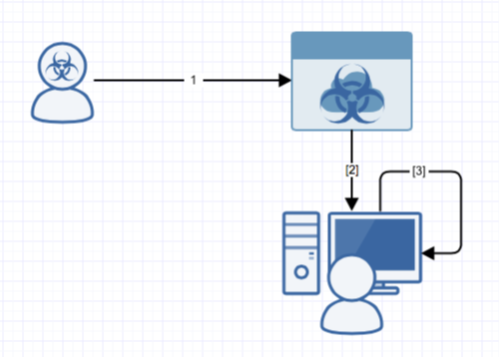
- The attacker compromises the site to link to the Exploit Kit landing page; the user may visit or be directed via an email link.
- The successful exploit causes the download and execution of CrypMIC server-side ransomware which beacons to the command and control server.
- The encryption of files occurs, whereby the victim is directed to a payment site for decryption keys.
Prerequisites
No prerequisites are required.
Vulnerability Description
A number of vulnerabilities may be utilized within Exploit Kits; however, no specific vulnerability is required once infection has occurred.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
The attacker must have exploited some other entry vector to allow the malicious files to become resident on the victim machine. Ensure that all relevant software is patched to the most up to date version.
Comments
0 comments
Please sign in to leave a comment.