Shutdown57 is a malicious server-side ransomware application written in PHP. Once the malicious PHP file is uploaded to a web server, it can be accessed and interacted with. By interacting with the web shell, the malicious user is able to cause it to encrypt files on the filesystem within the web server data directory. Currently, other than paying the ransom, there is no known way to decrypt files encrypted by the ransomware.
Exploitation
Stages
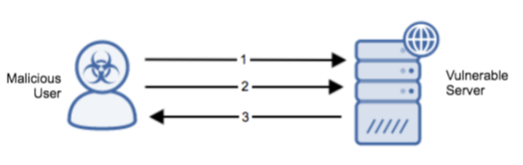
- The malicious user exploits an attack vector such as outdated software or a misconfigured server to install the web shell.
- The malicious user interacts with the web shell and allows the attacker to use web shell functions on the compromised webserver.
- A status is returned from the web shell indicating that its usage has been successful.
Prerequisites
The attacker must be able to send crafted packets to the target system.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
The attacker must have exploited some other entry vector to allow the malicious files to become resident on the victim machine. Ensure that all software is up to date to reduce the attack space for this vector.
Comments
0 comments
Please sign in to leave a comment.