The WordPress Front-end Editor plugin contains an unauthenticated file upload vulnerability. The 'upload.php' script is included as part of the Aloha 'draganddrop' plugin demo. The script checks all headers looking for the ‘X-File-Name’ header, creates a file with the specified name, then writes the contents of the POST body to that file and exits. Absolutely no file extension or MIME type validation is performed. This means that any file could be uploaded to the server and then accessed by an unauthenticated user.
Exploitation
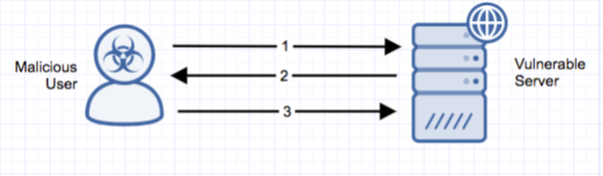
Stages
- An unauthenticated attacker sends a POST request containing PHP code and an ‘X-File-Name’ header to ‘…/wp-content/plugins/front-end-editor/lib/aloha-editor/plugins/extra/draganddropfiles/demo/upload.php’.
- The server responds with a ‘200 OK’ response and the filename is sent via the ‘X-File-Name’ header.
- The attacker makes a GET request for the uploaded filename located in the same directory as ‘upload.php’.
Prerequisites
The $HTTP_RAW_POST_DATA functionality in the PHP must be enabled via php.ini for the script to function (this functionality was deprecated in v5.6 and removed in PHP 7). Additionally, a WordPress instance running the front-end-editor plugin prior to version 2.3 is susceptible to attack.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Detection of this threat is provided via Alert Logic ActiveWatch for Web Security Manager service. Depending on your deployment of Web Security Manager, you will receive an incident (for out-of-band deployment) or the threat will be actively blocked and rejected (for the inline Web Security Manager Premier deployment) if an exploit attempt is observed.
Recommendations for Mitigation
To mitigate the vulnerability, upgrade to a non-vulnerable version of the plugin.
Comments
0 comments
Please sign in to leave a comment.