There is an arbitrary file upload vulnerability in the WordPress plugins ‘Powerzoomer’, ‘Slideshow Pro’, ‘Blaze Slideshow,’ and ‘Catpro gallery’. The file upload capability does not have restrictions on what types of files can be uploaded. The uploads are handled by a function defined ‘handle_admin_requests()’. The parent function is add_actions() which only requires the user to make a request to the administrative interface for the code to execute; therefore, the user does not need to be authenticated. This code is common amongst the four plugins mentioned previously. In this case, an unauthenticated attacker can upload a malicious file to the server via the category management section of the plugins.
Exploitation
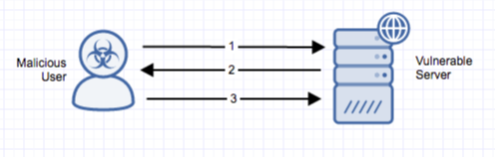
Stages
- A remote unauthenticated attacker sends a request to ‘/wp-admin/admin.php?page=(powerzoom) | cpr_manage’ uploading a malicious file to the server by creating a new category in the plugin, with the uploaded file as the category image.
- The server will respond with a WordPress error declaring the file is not an image, however the file has been uploaded to the WP upload directory ‘wp-content/uploads/(powerzoomer | blaze | catpro | slideshowpro)/<integer>_uploadfolder/big’.
- The attacker can access their file at the above directory structure by sending a GET request.
Prerequisites
The plugin must be installed on the victim’s system.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Detection of this threat is provided via Alert Logic ActiveWatch for Web Security Manager service. Depending on your deployment of Web Security Manager, you will receive an incident (for out-of-band deployment) or the threat will be actively blocked and rejected (for the inline Web Security Manager Premier deployment) if an exploit attempt is observed.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.