XMRig is a high performance Monero (XMR) miner. There is a CPU/NVIDIA-GPU/AMD-GPU version of the miner. The miner is equipped to run on both Windows and Linux (both x86 and x86_64). Remote attackers have either enticed users into downloading a powershell staging script onto their server or uploaded the script via a vulnerability (Oracle WebLogic vulnerability). When the script is executed, it downloads and unpacks the XMRig miner. Execution of the miner will see a spike in CPU usage as the miner utilizes processing power to mine Monero coins.
Exploitation
Stages
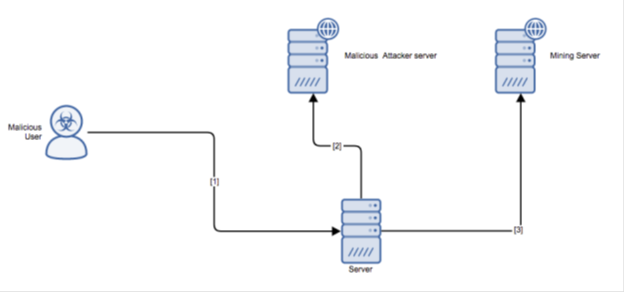
- The malicious attacker uploads a powershell staging script onto the victim’s server via an unknown vector (phishing email, vulnerability, etc.).
- When the powershell script executes, it downloads the miner from an attacker-controlled server onto the victim’s server.
- When XMRig miner is executed by the staging script, it begins to mine for Monero pointed at a specific mining server and wallet.
Prerequisites
The attacker must be able to send crafted packets to the target system.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.