There is an unauthenticated remote code execution vulnerability in certain versions of Apache Struts (Struts 2.0.1–Struts 2.3.33 and Struts 2.5–Struts 2.5.10). The vulnerability is caused by the unsafe use of writable expression values in FreeMarker content. A remote unauthenticated attacker can exploit this by adding OGNL content to a writable expression that is then submitted to an application for processing. The result of this attack allows attackers to execute arbitrary commands on the victim’s system.
Exploitation
Stages
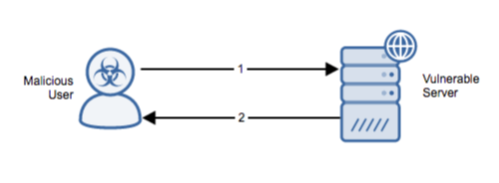
- The remote unauthenticated attacker injects OGNL expression into HTTP parameters that are running a vulnerable version of Struts.
- The OGNL expression is processed by the server and the attacker’s command is executed. Depending on the attack, the command may be reflected in the response.
Prerequisites
The attacker must ascertain whether the application is running a vulnerable version of struts and if the version is utilizing writable expression in FreeMarker tags.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Detection of this threat is provided via Alert Logic ActiveWatch for Web Security Manager service. Depending on your deployment of Web Security Manager, you will receive an incident (for out-of-band deployment) or the threat will be actively blocked and rejected (for the inline Web Security Manager Premier deployment) if an exploit attempt is observed.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.