The XAttacker PHP web shell is part of the XAttacker Website Vulnerability Scanner and Auto Exploiter. The tool has the ability to upload web shells, access databases, and exploit cPanel. The tool is written in Perl and contains exploits relating to WordPress, Joomla, Drupal, Prestashop, and Lokomedia. Most of the exploits relate to uploading the specific ‘XAttacker.php’ web shell. It is a relatively basic shell with the ability to upload files. It also runs the PHP function ‘php_uname()’ that returns the OS version of the victim’s system.
Exploitation
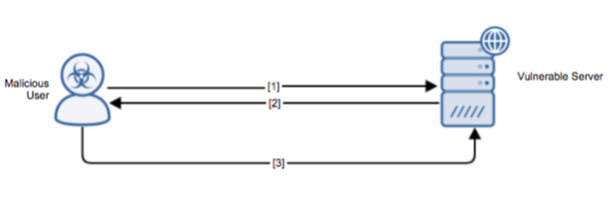
Stages
- A remote attacker attempts to upload or coerce a target system to download the XAttacker web shell.
- The HTTP response indicates that the shell has been uploaded.
- The attacker sends an initial request to the XAttacker web shell.
Prerequisites
The attacker must be able to send crafted packets to the target system.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
The attacker must have exploited some other entry vector to allow the malicious files to become resident on the victim machine.
Comments
0 comments
Please sign in to leave a comment.