Several SQL injection vulnerabilities exist within three Joomla mapping components: 'Zh BaiduMap' <=3.0.0.1, 'Zh GoogleMap' <=8.4.0.0, and 'Zh YandexMap <=6.2.1.0. All three components were developed by the same individual and use a common code base with identical task names and only minor variations in the backing database structure. The vulnerabilities exist as a result of unsanitized user-controlled input being used in the construction of a SQL query that is then executed on the server. Arbitrary SQL can be injected via the 'id' parameter. The use of the 'UNION' operator enables an attacker to perform additional sub-queries and return the results of those queries via the JSON array of data. The vulnerabilities can be used to exfiltrate a range of information from the database which could be used to facilitate further compromise of the target or theft of sensitive information.
Exploitation
Stages
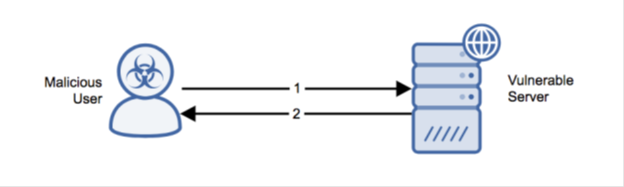
- A POST request is sent to a vulnerable server with a URI containing the required query parameters and an ‘id’ POST parameter containing SQL syntax.
- The server constructs and executes the compromised SQL query and returns portions of the result set via a JSON encoded array.
Prerequisites
The attacker must be able to send crafted packets to the victim system.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Detection of this threat is provided via Alert Logic ActiveWatch for Web Security Manager service. Depending on your deployment of Web Security Manager, you will receive an incident (for out-of-band deployment) or the threat will be actively blocked and rejected (for the inline Web Security Manager Premier deployment) if an exploit attempt is observed.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.