The shkilla malware is a low complexity Bash script used as the first stage in post-compromise. Samples contain edits, bugs, inefficiencies, and lines for the termination of unusual process names, suggesting that the author is actively updating the malware as he races to compete against rival miners. The malware maintains persistence with cron, uses XMRig for the mining of Monero, and attempts to propagate via SSH.
Exploitation
Stages
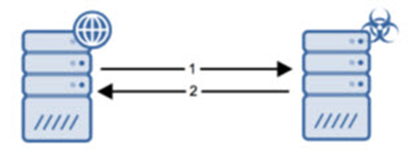
- The compromised server makes an HTTP request to download the malware.
- The malware is successfully downloaded onto the compromised server.
Prerequisites
The attacker must be able to upload the malware via some other misconfiguration or exploited vulnerability.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Ensure that all systems are up-to-date and secured such that attackers are not able to inject this code onto victim hosts.
Comments
0 comments
Please sign in to leave a comment.