DSI is a minimal web shell that will execute PHP code that is passed in an HTTP POST parameter. The web shell is obfuscated with junk characters inserted into function names and base64, which are then stripped out during execution.
Exploitation
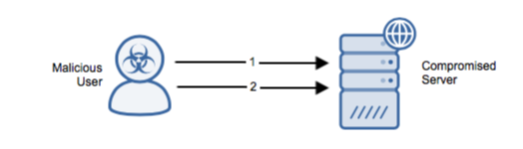
Stages
- The attacker uploads/downloads the DSI web shell to the server via an arbitrary vector.
- The attacker sends an HTTP POST request with PHP code contained within the cmd POST parameter. The server replies with an HTTP 200 OK response containing the output from the executed PHP.
Prerequisites
The attacker must be able to send crafted packets to the target system.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
The attacker must have exploited some other entry vector to allow the malicious files to become resident on the victim machine.
Comments
0 comments
Please sign in to leave a comment.