A vulnerability was found in the SyntaxHighlight MediaWiki extension. An attacker is able to create and inject arbitrary PHP objects via crafted <syntaxhighlight> tags. This is caused by a lack of sanitization when rendering highlighted content. This vulnerability affects any MediaWiki installation with SyntaxHighlight version 2.0 installed and enabled. Authentication is required if the wiki is set to 'private', and is not required if the wiki space is configured for public access.
Exploitation
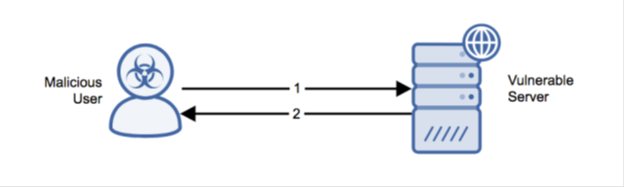
Stages
- The attacker makes an HTTP POST request to ‘/api.php’ containing a weaponized SyntaxHighlight tag.
- MediaWiki’s SyntaxHighlight plugin interprets the weaponized tag resulting in command execution on the target host.
Prerequisites
The public-facing host must be running MediaWiki with SyntaxHighlight 2.0 enabled with valid MediaWiki credentials or publicly configured MediaWiki installation.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
To mitigate the vulnerability, upgrade to a non-vulnerable version of the plugin.
Comments
0 comments
Please sign in to leave a comment.