The XDebug extension <= v2.6.0 for PHP is designed to expand the debugging capabilities of developers, including the ability to perform remote debugging. A misconfigured server, with ‘xdebug.remote_connect_back’ enabled, exposed to the internet could allow an unauthenticated remote attacker to trigger a debugging session using any IP via a simple web request. With a remote debugging session established, the attacker effectively has remote code execution (RCE) capabilities with which to establish persistence, exfiltrate data, or launch further attacks against the system or network.
Exploitation
Stages
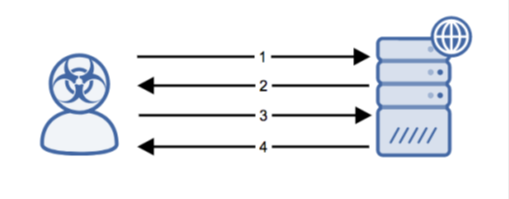
- The remote attacker sends an HTTP request to a PHP resource on the target server containing the XDebug parameter or cookie.
- The server makes an outbound DBGP connection to the attacker on port 9000 using the specified session identifier.
- The attacker executes DBGP commands to have malicious PHP code evaluated on the server.
- After the DBGP session is closed, the server sends the response to the original HTTP request.
Prerequisites
The attacker will exploit a web server running XDebug with remote debugging enabled.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Ensure that XDebug is not exposed to the public internet and ensure that ‘xdebug.remote_connect_back’ is disabled.
Comments
0 comments
Please sign in to leave a comment.