The autoload.js script is an exfiltration shell designed to capture login form entries and exfiltrate them to an attacker-owned C2 server via encoded curl requests. Conducted research has led to the discovery of five shell variants designed to capture and exfiltrate requests containing payment and user details. This shell has been observed in active Magento exploitation campaigns.
Exploitation
Stages
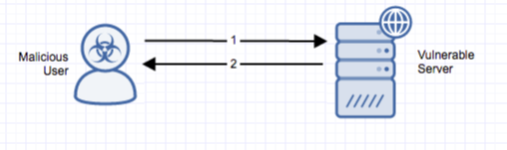
- A remote attacker compromises a Magento installation and manually implants the autoload.js script.
- The autoload script uses regex to parse incoming request payloads, and when a match is found, the request payload is exfiltrated to an attacker-owned C3 server using either bash curl commands or php-curl.
Prerequisites
The attacker must be able to send crafted packets to the target system.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
The attacker must have exploited some other entry vector to allow the malicious files to become resident on the victim machine.
Comments
0 comments
Please sign in to leave a comment.