Analysis of inversion of control on a recent Magento application affecting malware strain appears to have ties and similarities to MageCart. MageCart is the collective name for a group of attackers who skim personal data including credit card information from website checkout forms. Techniques include server side exfiltration using a PHP call to curl and client-side exfiltration using java script. The attacking group is known to target Magento installations using unknown vectors
Exploitation
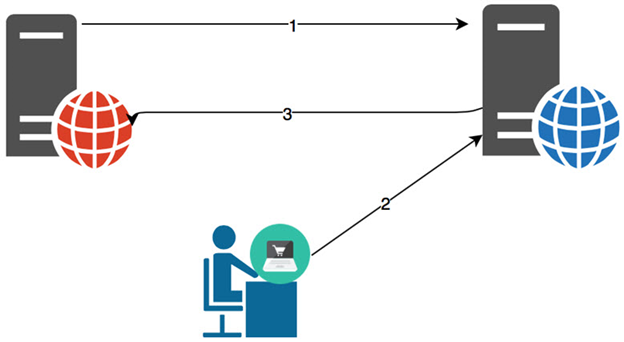
Stages
- An attacker compromises the server and installs malicious script.
- The attacker enters sensitive information during the checkout process.
- The compromised server exfiltrates sensitive information to the attacker.
Prerequisites
The attacker must be able to inject the malicious code onto the web server through another vulnerability or exploit.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
The attacker must have exploited some other entry vector to gain access to the local victim host. Ensure that all software on internet-facing hosts is up-to-date.
Comments
0 comments
Please sign in to leave a comment.