The remote method invocation (RMI) registry of Java SE versions (including and prior to 6u25, 5u29, and 1.4.2_31) are vulnerable to the remote loading of Java classes through the RMI activation service. Attackers can invoke methods of the RMI Distributed Garbage Collector with a serialized object annotated with a URL to exploit this vulnerability.
Java SE versions 7u24 and before fail to validate serialized remote objects passed with the RMI registry.bind call. This leads to the deserialization and remote execution of the attacker code.
Exploitation
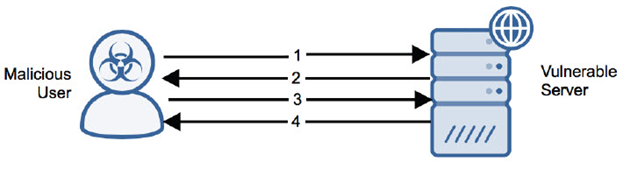
Stages
- The attacker sends the Java RMI header to the vulnerable server.
- The vulnerable server replies with the Java RMI acknowledgment.
- The attacker sends a Java RMI call with a serialized object that will exploit the server on deserialization.
- The vulnerable server replies with Java RMI ReturnData with a return value indicating that the exploit was accepted and deserialized.
Prerequisites
The attacker can exploit remotely and without authentication.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.