DoppelDropper has been used in a campaign against the Drupal CMS and is vulnerable to CVE-2018-7600. The malware consists of two dropper stages followed by the download and execution of XMRig. Both stages are still in active development.
Exploitation
Stages
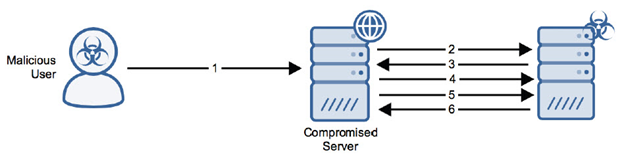
- The attacker uploads the Bash script to the compromised server via remote code execution.
- The Bash script runs on the compromised server and sends an HTTP GET request to the attacker’s server.
- The attacker’s server sends an HTTP 200 OK response with the second stage (the PRCS binary).
- The second stage sends an HTTP POST request from the compromised server containing the hostname and number of processors.
- The second stage sends an HTTP GET request from the compromised server.
- The attacker’s server sends an HTTP 200 response with the third stage (the XMRig binary).
Prerequisites
The attacker must be able to send crafted packets to the target system.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
The attacker must have exploited some other entry vector to allow the malicious files to become resident on the victim machine.
Comments
0 comments
Please sign in to leave a comment.