Pacu is an open source Amazon Web Services (AWS) exploitation framework, designed for offensive security testing against cloud environments. Created and maintained by Rhino Security Labs, Pacu allows penetration testers to exploit configuration flaws within an AWS account, using modules to easily expand its functionality. Current modules enable a range of attacks, including user privilege escalation, backdooring of IAM users, attacking vulnerable Lambda functions, and more.
Exploitation
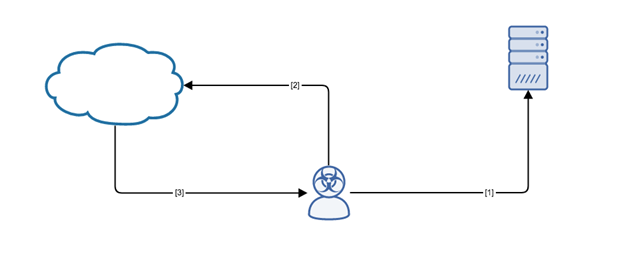
Stages
- The attacker retrieves AWS access keys through OSINT/nefarious methods.
- The attacker utilizes the AWS Pacu framework to access a certain account. From there, any number of modules can be used to carry out the objectives of the attacker (such as data exfiltration and account compromise).
- The response is returned to the attacker to indicate success or failure depending on the module.
Prerequisites
The majority of the modules require AWS access keys to be successful.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
Detection of this threat is provided via the Alert Logic ActiveWatch for Log Manager™ service. Log messages are produced by the vulnerable system when an exploit of this type is leveraged. An incident will be generated in the Alert Logic console if these log messages are observed.
Recommendations for Mitigation
- Do not store access keys in publically accessible places (such as GitHub).
- Follow AWS security practices relating to the rotation of access keys.
- Check S3 buckets to ensure that they are not publically available.
Comments
0 comments
Please sign in to leave a comment.