Core dump files contain the working memory state of a program at the time of abnormal termination or crash. Core dumps provide an invaluable source of information and insight for diagnosis and debugging purposes. The information contained within the core dumps is potentially just as valuable to an attacker who may be able to extract sensitive information like credentials or user data. Default Linux installations will often write the core dump file to the current working directory of the program which, if externally accessible, poses a security risk. Applications such as the Apache Web Server can be configured to write core dump files to specific locations. This may include externally accessible locations to enable remote debugging.
Exploitation
Stages
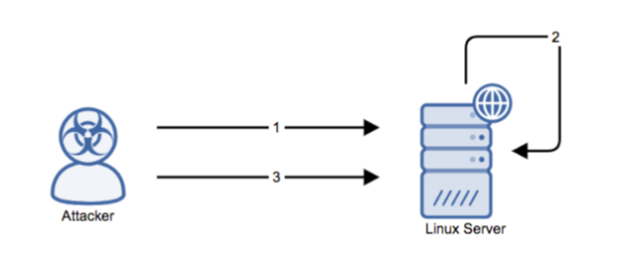
- A Linux application is forced to crash using a remote exploit or in the course of normal operation.
- The application generates a core dump file which is written to a remotely accessible location.
- The attacker retrieves the core file containing potentially sensitive information.
Prerequisites
The following prerequisites are subject to malicious attack:
- The Apache web server with ‘CoreDumpDirectory’ directive is pointing to a remotely accessible location.
- The Linux installation is configured to write core dump files to CWD or a remotely accessible location.
- The Linux core file size limit is greater than zero (determined by using ‘ulimit –c’.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Ensure that core dumps are not written to a publicly accessible web location if they are necessary on a production system.
Comments
0 comments
Please sign in to leave a comment.