The Wolf PHP web shell is utilized by threat actors to carry out their objectives in the context of the web server. It contains functionality for command execution, file uploading, the ability to read various sensitive files, retrieving usernames and passwords, retrieving database configuration files, and adding a secondary shell (X-Shinobi) as a method of persistence. The secondary shell provides a lot of the same functionality but with additional functions like a bind shell, SMTP credential retrieval, and CPanel cracker. The attacker can upload this web shell via a vulnerability or misconfigured upload mechanism.
Exploitation
Stages
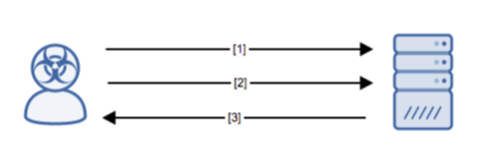
- The attacker uploads the shell to a vulnerable or misconfigured system.
- The attacker attempts to access the web shell functionality to carry out malicious objectives.
- The server responds by indicating its presence.
Prerequisites
The attacker must be able to send crafted packets to the target system.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
The attacker must have exploited some other entry vector to gain access to the local victim host. Ensure that all software on internet-facing hosts is up-to-date.
Comments
0 comments
Please sign in to leave a comment.