The Resin application framework is a Java application server and includes a high-performance webserver. The framework has a relatively small market share and is designed for speed and scale and is subsequently used by several high profile, high traffic sites. The framework includes functionality for viewing help files and documentation which accepts target files as URL query parameters. The information disclosure vulnerability in question arises from insufficient validation of the ‘file’ parameter, enabling the contents of arbitrary files to be viewed.
Exploitation
Stages
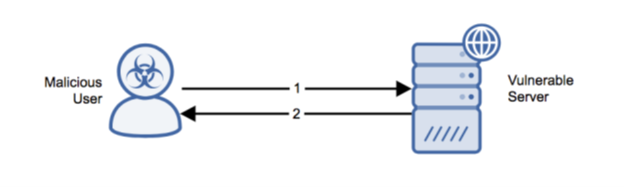
- An unauthenticated remote attacker passes an arbitrary JSP file via the file parameter to the ‘resin-doc/viewfile’ application path.
- The server responds with the contents, namely the source code, of the specified file.
Prerequisites
The attacker must be able to send arbitrarily crafted packets to a publicly accessible, internet facing endpoint.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.