The ‘WP Live Chat Support Pro’ plugin <= v8.0.07 for WordPress contains an arbitrary file upload vulnerability. The plugin appears to rely upon the ‘Content-Type:’ declaration contained within the file upload request to perform MIME type validation. An unauthenticated remote attacker can forge this value to contain a permitted MIME type while uploading a PHP script. The plugin helpfully returns the full path to the uploaded file when successful, allowing it to be requested and the contained PHP code to be executed.
Exploitation
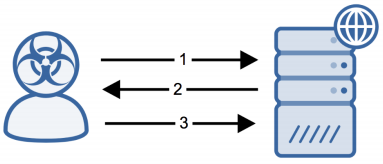
Stages
- A remote unauthenticated attacker submits a file upload POST request using the WP Live Chat Support plugin REST API endpoint.
- The server responds with a 200-response containing the full path to the uploaded file.
- The attacker requests the uploaded file, resulting in remote code execution on the target server.
Prerequisites
The attacker must be able to send crafted packets to the target system.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Upgrade to a non-vulnerable version to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.