Exploitation of a vulnerability that allows for information disclosure can return file contents from the server. A well-known attacking tactic is to contact or exfiltrate the contents of the /etc/passwd file, since it contains sensitive user information. This data could be used to more successfully execute a brute force or allow password stuffing to be more successful.
Exploitation
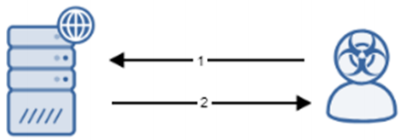
Stages
- An attacker sends a request to a web server taking any form but containing the string /etc/passwd.
- The server responds with data that appears to be disclosure of /etc/passwd.
Prerequisites
Any parameter may be affected in this type of attack. This attack is unauthenticated.
Alert Logic Coverage
Alert Logic® has evaluated its customer base for exposure to the exploit and has developed signatures for mitigating the threat depending on the security service in place.
The Network-Based Intrusion Detection System (IDS) has been updated with the new signatures for this exploit when detected via Alert Logic Threat Manager™. If this signature is detected, an incident is generated in the Alert Logic console.
Recommendations for Mitigation
Apply security patches to the programs to mitigate this vulnerability.
Comments
0 comments
Please sign in to leave a comment.