Many organizations that have seen growth and subsequent business change do not necessarily scale IT governance and controls in line with this growth. This often results in immature IT processes and policies that introduce risks to the organization - risks that can be avoided when addressed with an appropriate framework. With the introduction of the General Data Protection Regulation (GDPR) in May 2018, there is growing pressure on organizations to tighten privilege controls to avoid hefty fines and damage to reputation. Privileged access management (PAM) reduces the risk of data breaches caused by insider attacks and mass malware infections.
In This Article
Who needs this information?
Information system managers, risk managers, system administrators, audit professionals, and those with a general interest in IT governance and compliance will find this information particularly helpful.
What problems can privileged access management address?
Privileged access management can assist with privilege vulnerabilities, misconfigurations, unauthorized privilege escalations, spear phishing of privileged users, watering hole attacks, and "fat finger" incidents.
Use Case Scenario
Consider the following example, which illustrates that privileged access management could have prevented this issue.
Paul is an engineer writing code for a new application for his company. He has held on to several admin rights from his previous job as a desktop admin, and his normal user account has local admin access to every workstation in the office and to several file shares.
Paul uses GitHub and, one day, is directed to a fake version of GitHub after he mistypes the domain name. Unaware that he has fallen victim to "typo squatting," he enters his credentials - the same as his domain credentials - and finds that they do not work on the fake site. He closes the browser and heads to a meeting.
Later that day, several users in Paul's office complain that their computers are locked and that they cannot access anything. The owner of the fake GitHub site has struck lucky with Paul and used his privileged account to deploy ransomware across the office.
There are several ways that Paul's scenario could have been prevented, all to do with PAM:
- Separation of duty - Admin privileges like those Paul possessed should not be available on a user's standard account. Instead, a dedicated admin account should be provided with limited, or no, access to the internet.
- Joiners / movers / leavers - A robust movers process would have ensured that Paul had his admin access removed when he left his previous role as desktop admin.
- Privileged access education - Paul should have been made aware of the risks of using his domain credentials on external websites, especially those that are frequently breached or that are commonly the target of watering hole attacks and typo squatting.
Approaching Privileged Access Management
There are many approaches to privileged access management, but we will focus on three key life cycle steps that can be repeated until an organization has achieved a suitable level of control or mitigated a satisfactory amount of risk - Prepare, Protect, and Operate & Monitor.
Prepare
The Prepare phase is where you will determine what you are protecting, determine what frameworks and tools you may wish to introduce, and ensure that you have a consistent and well-communicated definition of privileged access. During the Prepare phase, you must also identify which users and groups should be targeted in later stages.
Protect
The Protect phase is where you will begin removing rights, implementing secret rotation, enforcing multi-factor authentication, and providing training. You can also introduce PAM tools and monitoring requirements at this stage.
Operate & Monitor
At this final stage, you should have your initial protection controls and operation procedures, such as change requests for adding and removing rights, in place. Monitoring output should generate incidents for your information security team, and you should have a tailored incident handling process in place to ensure quick response to changes in privilege.
Prepare
Consider the following during the Prepare phase:
Strategy
- PAM must align with the organization's security strategy
- The impact of poorly managed privileges must be highlighted as a risk to overall business strategy, as businesses can only truly assess risk when they understand where their key data assets are located and how they are exposed
Objectives
- Provide a clear definition of what constitutes privileged access
- Determine what systems are in scope for PAM; there is no shame in starting small and building up as you repeat these phases
- Identify which access channels are being targeted as part of PAM (e.g. user accounts, interfaces, etc.)
- Ensure that privileged access tools are identified and assessed
- Classify data assets and design access roles to be implemented during the Protect phase
People
- Identify who will be impacted by PAM
- Identify who will own the various elements of PAM (e.g. credentials, life cycles, policies, etc.)
- Identify what skills are needed to implement PAM and run the process as business as usual
- Ensure feedback channels are available for colleagues and stakeholders
Integrations
- Consider introducing PAM as a security deliverable for all deployed solutions within your organization's software development life cycle. This can be achieved in several ways:
- Quality controls - Code analysis and user testing may highlight bugs or misconfigurations that allow for elevated privileges
- Security quality gates - Ensure that no solution can be shipped until security gates are satisfied or until there are suitable mitigations in place
- Align to a DevSecOps culture - Allow security to be at the center of solution development
- Integrate PAM with identity and access management and HR practices
- Considering joiners, movers, leavers, and re-joiners
- Encourage a culture of "just enough access," also known as "least privilege"
- Introduce change management as a mechanism for managing privileged access changes and approvals
- While the process is new, all amendments to privileged groups should be heavily scrutinized by peers
- Once the process is established and proven to work as intended, change requests can be approved by default if the requester has met pre-defined acceptance criteria. This reduces the time spent raising arduous requests and the overhead on approvers who may not be available to review changes.
Protect
In the Protect phase, you will begin implementing protection measures for your organization. To do this, you must implement controls that are appropriate for your data assets, depending on how you have classified them.
Controls may vary depending on your organization's appetite for risk. For example, if a control is deemed business-impacting because it takes too long or costs too much to implement, ensure that senior sponsors are aware of this when making the decision not to implement that control.
Review this non-exhaustive list of controls your organization could choose to implement:
- Access review
- Password / secret rotation
- Multi-factor authentication
- Expiring access
- Role-based access controls
- Physical controls
- Network access control lists
- Access channel management
- Admin accounts - separation of duty
- Training / champions
- Account lockout
- Account expiration
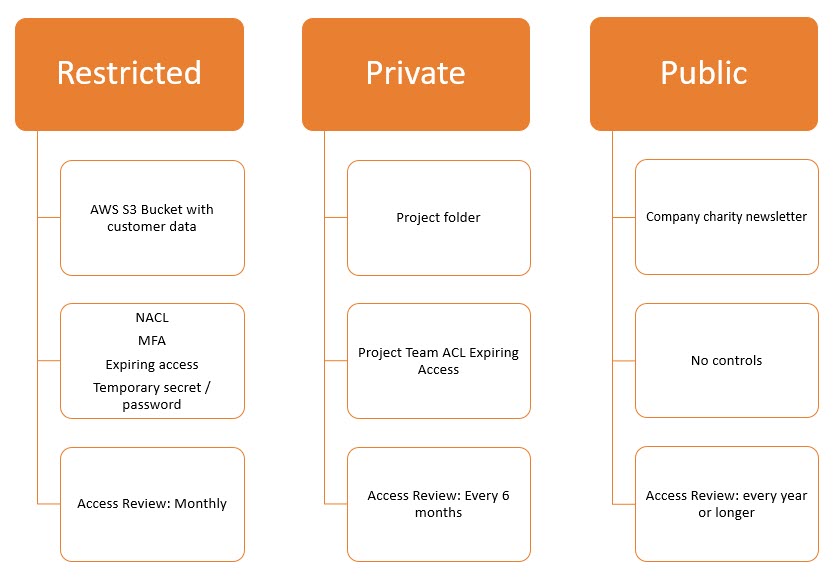
The below chart is an example of how controls can be applied to different data classification levels. The classification itself may take place in the Prepare phase, after data asset discovery.
Tooling for Protection
Many options are available as you consider tooling for PAM. It is important to choose a tool that will scale in line with your evolving protection requirements.
AWS Secrets Manager is a good example of one tooling option that scales well. It is a fully scalable cloud-native tool that allows administrators to safely give access to secrets. It also removes the need to store credentials in code and provides auto-rotation policies that can be applied to all secrets.
Gartner has produced a Magic Quadrant for PAM tooling that can help you choose the best tools for your organization.
Protection Considerations
Protection is not perfect. Consider the following risks and ensure that any control you put in place is not rendered ineffective by a vulnerability or misconfiguration:
- SMS multi-factor authentication is sometimes considered unsafe for high-value targets like privileged users and executives. Some believe it should no longer be used due to the rise of SIM swapping attacks against those high-value targets. Alternatives to multi-factor authentication may include hardware tokens and authentication apps for mobile devices. You can find information about multi-factor authentication online, such as in this article.
- Utilizing admin accounts is one of the best ways to reduce risk of privileged user compromise, but only if done correctly. Domain administrator accounts should be given no access to communicate with the outside world - that means no email and no access outside of the corporate network.
- Password / key rotation has been a topic of conversation in many organizations and forums as the result of guidance published by the National Cyber Security Centre. There are strong arguments for and against rotation; however, these arguments must be taken in the context of the information you are rotating. The National Cyber Security Centre states:
"Regular password changing harms rather than improves security.
Forcing password expiry carries no real benefits because:
- The user is likely to choose new passwords that are only minor variations of the old
- Stolen passwords are generally exploited immediately
- Resetting the password gives you no information about where a compromise has occurred
- An attacker with access to the account will probably also receive the request to reset the password
- If compromised via insecure storage, the attacker will be able to find the new password in the same place."
This information is in the context of the general user population and not privileged users or privileged service accounts and other secrets. You should consider secret rotation necessary for these accounts, combined with additional measures such as multi-factor authentication and account lockouts.
Security Champion vs. Security Training
Security training has its merits, but it must be an engaging and rewarding experience for the audience - presentation slides that encourage privileged access management behaviors can be easily forgotten the moment students leave the room.
Security champions offer a different approach:
- Peers may be more likely to take best practice advice from peers they know and trust
- Champions reduce the total cost overhead of PAM tool training by training a champion once, who can then train peers
- Champions gain experience as teachers and advocates for business change
- Champions can be trained on several security topics
Considerations when using security champions:
- Champion programs require a certain level of management to account for champions leaving or switching teams
- Rewards or incentives must be aligned correctly to encourage champion volunteers
Operate & Monitor
Currently, log correlation engines and big data analytical tools are in abundance and are not the focus of this section. Instead, we will discuss common event codes to use for alerting and forensics, as well as available audit tools and AWS-native threat detection resources.
What to Monitor
Windows provides a large pool of useful event codes for monitoring the security of endpoints, groups, and users; however, a subset of these event codes are particularly useful for PAM. The following is a list of event codes you can use:
Learn more about event IDs with the following external resources:
| ID | Error Name | PAM Usage |
| 4740 | Account Lockouts | Alert on privileged account compromise |
| 4728, 4732, 4756 | User Added to Privileged Group | Monitor addition of access rights |
| 4735 | Security-Enabled Group Modification | Monitor integrity of groups and search for attacker persistence |
| 4724 | Successful User Account Login | Monitor the user of privileged accounts |
| 4625 | Failed User Account Login | Indicator of brute force attack against privileged accounts |
| 4720 | A user account was created | Indicator of persistence / insider abuse |
| 4726 | A user account was deleted | Indicator of malicious insider potentially deleting other privileged, VIP, or service accounts |
- Ultimate IT Security - Windows Security Log Events
- PETRI - Monitoring Windows Event Logs for Security Breaches
- Spiceworks - What Windows Event IDs do you monitor?
Linux
Linux monitoring capabilities may vary depending on what distribution you are using, but you are never far away from a package that will allow you to easily set up audits. For example, CentOS comes with audit and audit-libs. See the below example of monitoring for privilege use and abuse with CentOS.
Audit Example
File monitoring rules can be added from auditctl. Below is an example of enabling auditing for the /etc/passwd file:
auditctl –a exit,always –F path=/etc/passwd -F perm=wa
In this example, “perm=wa” is used to indicate wanting to write log write actions (w) and attribute changes (a). Run ausearch to locate actions against the passwd file:
Ausearch –f /etc/passwd
time->Wed Sep 18 15:17:25 2019
type=PATH msg=audit(1395152245.230:533): item=0 name=”/etc/passwd” inode=137627 dev=fd:00 mode=0100644 ouid=0 ogid=0 rdev=00:00 obj=system_u:object_r:etc_t:s0 nametype=NORMAL
type=CWD msg=audit(1395152245.230:533): cwd=”/etc/audit”
type=SYSCALL msg=audit(1395152245.230:533): arch=c000003e syscall=188 success=yes exit=0 a0=d14410 a1=7f66eec38db7 a2=d4ea60 a3=1c items=1 ppid=1109 pid=4900 auid=0 uid=0 gid=0 euid=0 suid=0 fsuid=0 egid=0 sgid=0 fsgid=0 tty=pts0 ses=2 comm=”vi” exe=”/bin/vi” subj=unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023 key=(null)
The ausearch output gives you some useful information on what has happened to the file, such as:
- The command used: exe’”/bin/vi”
- The current working directory where the action took place: cwd=”/etc/audit”
- The target file: name=”/etc/passwd”
- The syscall ID: syscall=188
Use auditctl in a similar way to monitor all actions taken using root:
auditctl -a exit,always -F arch=b64 -F euid=0 -S execve -k root-commands
auditctl -a exit,always -F arch=b32 -F euid=0 -S execve -k root-commands
Once the rule is in place, the ausearch command can be used to retrieve results:
ausearch –k root-commands
Below, in bold, you can see that this root user has used apt to install th eGIMP image editor:
time->Tue Sep 17 10:10:17 2019
type=PROCTITLE msg=audit(1568729417.178:1170): proctitle=6170742D67657400696E7374616C6C0067696D70
type=PATH msg=audit(1568729417.178:1170): item=2 name="/lib64/ld-linux-x86-64.so.2" inode=1839575 dev=08:01 mode=0100755 ouid=0 ogid=0 rdev=00:00 nametype=NORMAL cap_fp=0 cap_fi=0 cap_fe=0 cap_fver=0 cap_frootid=0
type=PATH msg=audit(1568729417.178:1170): item=1 name="/usr/bin/apt-get" inode=1849799 dev=08:01 mode=0100755 ouid=0 ogid=0 rdev=00:00 nametype=NORMAL cap_fp=0 cap_fi=0 cap_fe=0 cap_fver=0 cap_frootid=0
type=PATH msg=audit(1568729417.178:1170): item=0 name="/usr/bin/apt-get" inode=1849799 dev=08:01 mode=0100755 ouid=0 ogid=0 rdev=00:00 nametype=NORMAL cap_fp=0 cap_fi=0 cap_fe=0 cap_fver=0 cap_frootid=0
type=CWD msg=audit(1568729417.178:1170): cwd="/home/user"
type=EXECVE msg=audit(1568729417.178:1170): argc=3 a0="apt-get" a1="install" a2="gimp"
type=SYSCALL msg=audit(1568729417.178:1170): arch=c000003e syscall=59 success=yes exit=0 a0=559fc43d5460 a1=559fc3e56600 a2=559fc3e75310 a3=fffffffffffff878 items=3 ppid=1564 pid=32511 auid=1001 uid=0 gid=0 euid=0 suid=0 fsuid=0 egid=0 sgid=0 fsgid=0 tty=pts0 ses=3 comm="apt-get" exe="/usr/bin/apt-get" subj==unconfined key="root-commands"
Amazon Web Services
Amazon Web Services (AWS) provides security notifications via GuardDuty. These notifications are categorized into several "findings" types. See the below example of utilizing the privilege escalation finding and other AWS services to automatically correct changes to IAM users.
Findings Example
The privileged escalation finding type is triggered when a principal in your AWS account assigns themselves a highly permissive policy. This can indicate a malicious insider or a compromised account. Frequently checking Amazon GuardDuty and waiting for this finding type may be considered inefficient, but you won't want to miss this information when it is triggered. Consider automation options in order to reduce the potential damage this account could cause. We will walk through a rough view of how this can work:
- A principal user assigns itself high privileges
- The privileged escalation GuardDuty finding is triggered
- A CloudWatch event rule triggers a Lambda function and SNS topic
- The Lambda function automatically removes the privilege and disables the principal user
- SNS sends an email notification to your SOC
This concept can be applied to many AWS security use cases, but there are several findings that are specifically helpful for PAM and that can also be automatically remedied:
- Privileged user consuming resources for personal gain
- Detecting and blocking brute force attacks against privileged accounts
- Reversing malicious network changes - ingress / egress
- Repairing policy changes - password / logging
AWS also provides a free tool that allows for proactive monitoring of permissions. Administrators can use the Policy Access Advisor to audit IAM privileges across an AWS account.
The objective of this information is to help you lay down a basic approach to PAM within your own organization, as well as to explain how to use different technologies to achieve compliance and security goals. There is no right answer to PAM, and different organizations will have to tweak their approach to suit their own objectives.
Comments
0 comments
Please sign in to leave a comment.