Alert Logic® now offers Web Log Analytics capabilities, which enhance our web application threat detection capabilities by adding a log-based threat detection and solving the visibility issue caused by modern transport encryption.
Alert Logic Web Log Analytics (WLA) is a log-based application attack detection solution that balances application protection against the continued onslaught of application attacks. A combination of anomaly detection, ActiveRules signatures, and advanced correlations provide coverage for much of the OWASP Top 10.
WLA is available for Managed Detection & Response customers with Professional and Enterprise entitlements.
Role of WLA in Web Application Security
WLA is a complementary technology to the Alert Logic intrusion detection system (IDS) capability (which uses telemetry from network) and the Alert Logic web application firewall (WAF) (which is situated in-line in the traffic path, between the client and the web application).
Compared to IDS web attack coverage, WLA’s advantages include deployments requiring less components on-site, the ability to reach a wider set of assets, and no dependence on decryption of traffic to provide visibility—which is becoming harder and harder due to the use of perfect forward secrecy ciphers in HTTP encryption. The price to pay for this is that the telemetry data is less complete – web log analytics are based on web logs, which do not include the full post requests and do not contain the full response of the server. This makes it difficult to assess whether an attack was successful or not.
Lastly, the WLA solution does not have a proactive ability to block an attack before it arrives at the attacked server–for that level of protection, Alert Logic recommend using our WAF solution.
In summary, no single technology is a silver bullet in security—and this is true for web application security, as well. To combat this, Alert Logic combines network IDS-based web application security with log-based web application security and WAF technology to support customer needs and balance risk appetite with configuration and deployment overhead.
Web Log Analytics Incident Coverage
Alert Logic can detect a wide range of incidents with WLA:
- Web recon - Clear enumerating or attack activity detected
- Attack generating 500-type server errors - Attack activity generating 500-type error responses from targeted web server
- Access to unauthorized resource - Injection or Remote Command Execution followed by access to potentially uploaded (anomalous) resource indicating upload and access to web shell
- Access to anomalous resource - Access to URL paths that are anomalous
- Attack targeting specific vulnerabilities - Very specific, surgical detections for exploits against known vulnerabilities
- Vulnerability scan - Web server attack observation indicative of a vulnerability scan from a source known to be a provider of information security auditing services
- Unauthorized vulnerability scan - Web server attack observation indicative of a vulnerability scan from a source not known to be a provider of information security auditing services
- Internal vulnerability scan - Web server attack observation indicative of an internal vulnerability scan (including by Alert Logic) from within your network
Incident Review and Handling
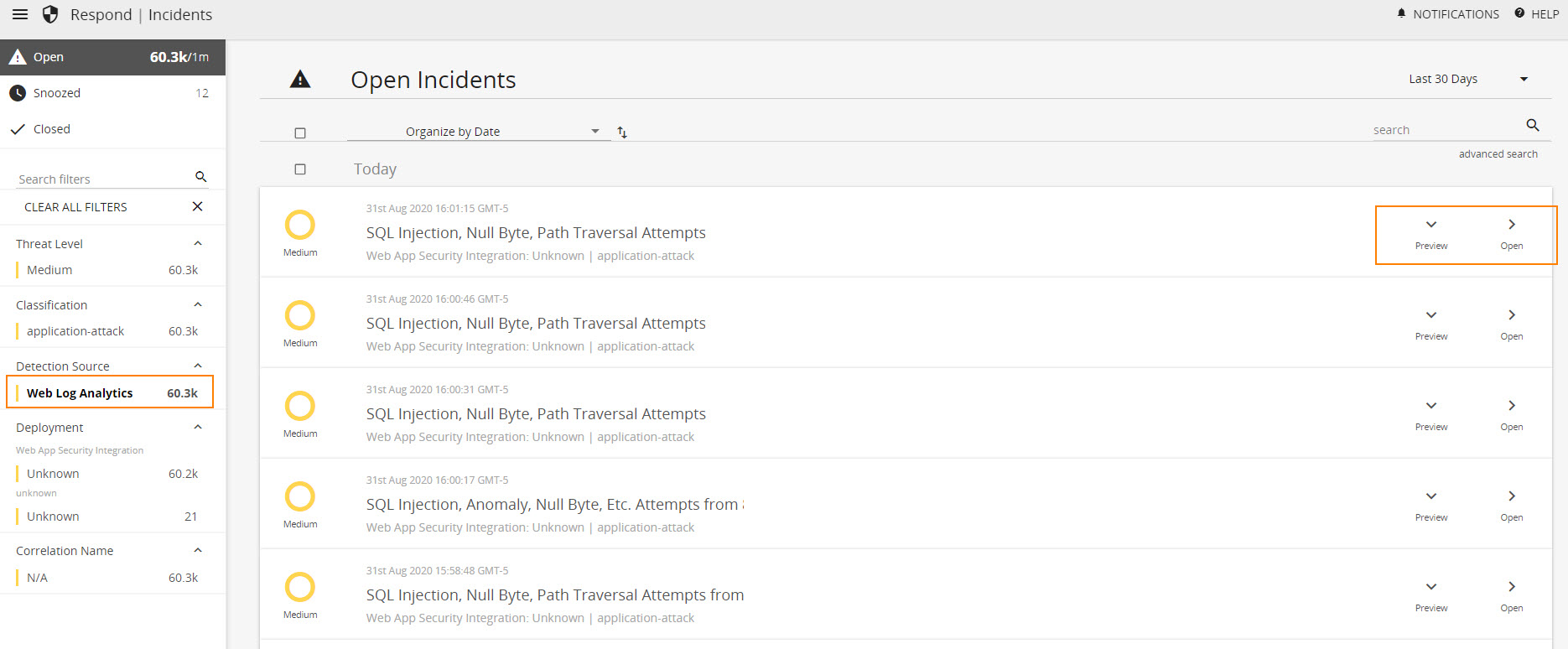
Incidents generated from WLA can be viewed and investigated within the Alert Logic console at Respond > Incidents > filter by Web Log Analytics. Information available for each incident includes an investigation report, recommendations for mitigation, and evidence of potential attack.
Note: WLA incidents are auto-escalated to customers as a Medium- or Low-severity threat.
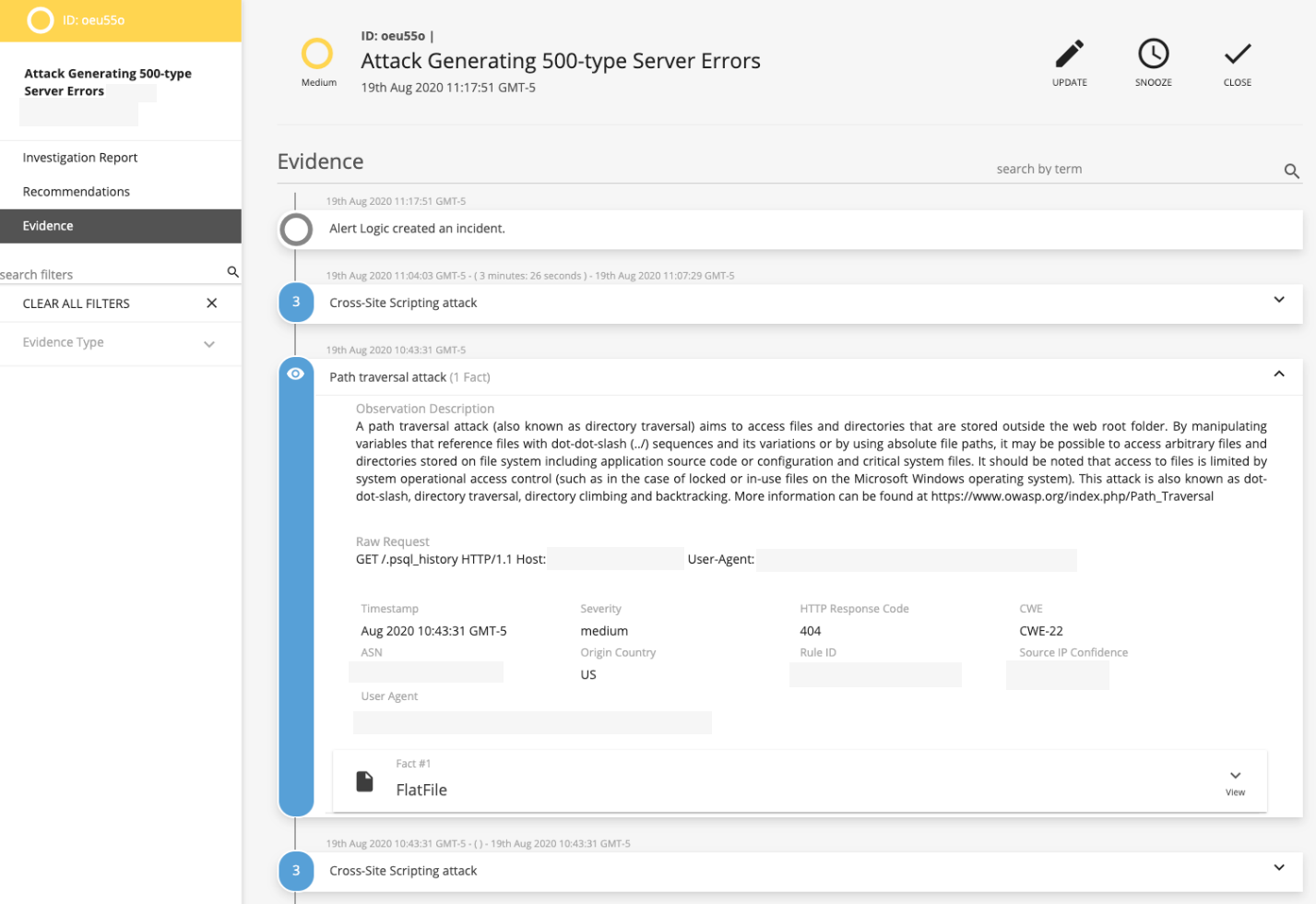
The investigation report will summarize key information to help you assess the attack–what web application or virtual host was impacted, which attack types were used, what user-agents were involved, and what weakness categories (CWE) were attacked. It will also show detailed information about the latest individual violation that caused the incident to trigger.
Recommendations will provide references to the weaknesses being exploited and how to address them in your environment.
Evidence
The Evidence section will show the individual observations that cumulatively led to the generation of an incident. Each of the observations were triggered because of observed patterns in log files, and you can click down all the way into the log file to validate the actual logged request.
Web Log Analytics Dashboard
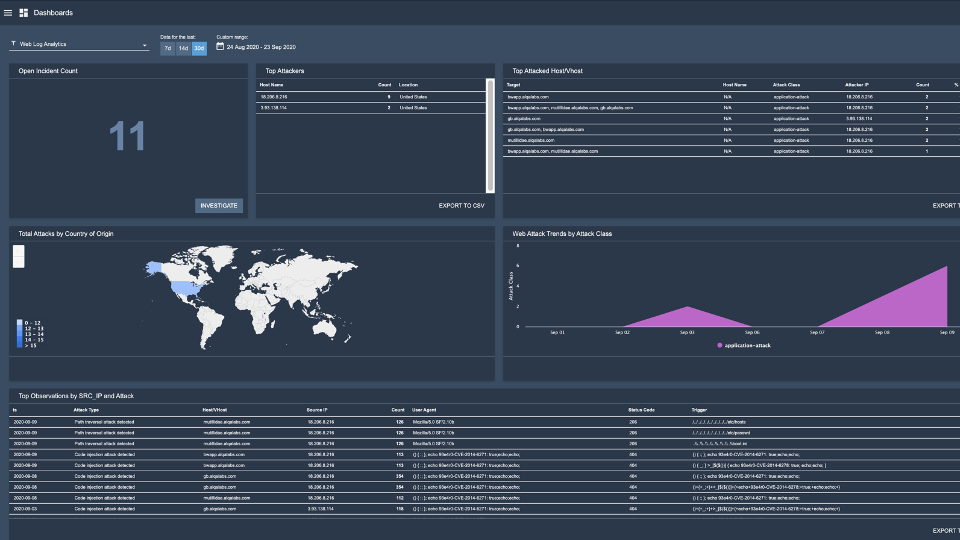
A Web Log Analytics dashboard is now available in the Alert Logic console at Dashboards > Web Log Analytics. This dashboard provides near-real-time visibility into your busiest attackers, allows you to prioritize efforts on your most attacked applications, and provides information on the geographical origin of attacks. Information such as Open Incident Count and Top Attackers is available within this dashboard, and many data points allow for further investigation.
For more details around the WLA dashboard, see our Web Log Analytics Dashboard documentation.
Access Log Format Requirements
While configuration changes are not required for customers to receive value from WLA, applying the Alert Logic-recommended configuration allows for maximum value, including the ability to utilize automated response capabilities and the most robust anomaly detection.
Supported default log formats for web servers include Common Log Format and IIS log file format.
Available WLA parsers include:
- combined_proxy – Apache, Nginx Common Log Format
- iis_default – IIS, IIS log format
- iis_custom – W3C extended log format
- alb – AWS application load balancer log format
- wsm – Alert Logic Web Security Manager deny logs
- wla_access_logs (preferred configuration) - support for Apache, Nginx, and IIS (filebeat)
For full details and guidance on WLA configuration, see our Web Log Analytics Configuration documentation.
For more information on Web Log Analytics, see the following Alert Logic documentation:
Comments
0 comments
Please sign in to leave a comment.