As a Managed Detection & Response (MDR) provider, Alert Logic continuously identifies threats and investigates exposures to add to our growing library of signatures. While this is an ongoing, daily effort for our Threat Intelligence and Security Operations Center (SOC) teams, occasionally an urgent security issue arises that needs to be addressed immediately. These urgent security issues are declared as “Emerging Threats” and treated with utmost urgency, requiring immediate action from teams across Alert Logic to keep our customers secure and informed.
This article will describe how a security issue becomes an Emerging Threat, what happens when an Emerging Threat is declared, what customers can expect from Alert Logic, and proactive measures customers can take to keep informed.
In This Article
- What is the criteria for an Emerging Threat?
- What happens once an Emerging Threat is declared?
- What if I have questions about an Emerging Threat?
What is the criteria for an Emerging Threat?
Alert Logic reviews and addresses high-risk and critical threats every day; however, few of these are declared as an Emerging Threat. As the threat landscape evolves and changes, the criteria to declare an Emerging Threat must also change. Currently, Emerging Threats generally share one or more of the following criteria:
- New Very Critical Risk vulnerability, with available or easy-to-build exploits
- New availability of exploits for an existing high-risk vulnerability
- Alert Logic telemetry showing active attacks against customer base
- Ongoing, large-scale campaign using a few specific exploits or vulnerabilities
- Widespread news coverage of a vulnerability or exploit that is concerning customers
- New prolific wave of ransomware targeting older vulnerabilities
For example, the SolarWinds Orion hack enabled an unprecedented attack on U.S. government and corporate networks with widespread news coverage and was immediately identified as an Emerging Threat. However, not all Emerging Threats are news headlines. In February 2021, an Emerging Threat was declared for a remote code execution vulnerability in VMware vCenter Server due to the high-risk level for this vulnerability and the common use of VMware. For more examples of past Emerging Threats, refer to the Emerging Threats section of our Knowledge Base.
What happens once an Emerging Threat is declared?
Alert Logic has developed a tried and tested framework for handling these Emerging Threats to provide coverage and alert customers as soon as possible. When an Emerging Threat is declared, a series of actions are taken in response, including detailed analysis, content creation, threat hunting, and communication.
Analysis and Content Creation
Even before an Emerging Threat is officially declared, the Threat Intelligence team begins researching the new exposure to understand the threat. This process includes:
- Gathering intelligence about the threat in question
- Recreating vulnerable environments to test potential exploits
- Developing and or running proof of concept exploits against vulnerable systems
- Releasing telemetry signatures to potentially capture malicious traffic associated with the threat
Once the team begins to understand the parameters of the threat, coverage and detection creation starts. Based on the nature of the vulnerability, coverage may be created for:
- Log Management – telemetry signatures to detect exploitation
- Network IDS – telemetry signatures and specific signatures to detect exploitation
- Vulnerability scanning – authenticated and/or unauthenticated coverage to identify vulnerable assets
- Web Application Firewall – patches to detect and/or block exploitation
When this content is created, it goes through an expedited release process to provide detection and coverage to customers as soon as possible. Some coverage is often released within 24 hours of identifying an Emerging Threat, and additional coverage is added as new information is learned about the threat.
As part of this process, internal teams also assess our own environments and infrastructure for vulnerability. If it is determined vulnerabilities exist, mitigation steps are taken to keep Alert Logic appliances, agents, and customer data secure.
Threat Hunting
When an Emerging Threat is identified, the SOC initiates targeted Threat Hunts, which entail creating and deploying custom telemetry signatures, dashboards, and tooling to best approach the active threat. The primary objectives of these hunts are to identify the breadth of the threat, risks to our customers, and active indicators of compromise and/or attack.
Note: Alert Logic analysts can only identify indicators of exploitation within areas where we have visibility into your environment. If you want to expand this visibility to obtain more detection coverage, contact your Customer Success Manager.
Communication
As the research and content creation takes place, communications go into development simultaneously. This communication can come in many forms based on the severity and nature of the threat.
- Knowledge Base Article
A Knowledge Base article is written for every Emerging Threat that is declared. This article is generally released within 24 hours of declaring an Emerging Threat and contains what we know about the threat so far, what coverage we have or intend to have, and recommendations for mitigation. This article is then updated as we release additional detection and coverage, as well as if we learn any significant new information about the threat, such as the release of patches from an affected vendor.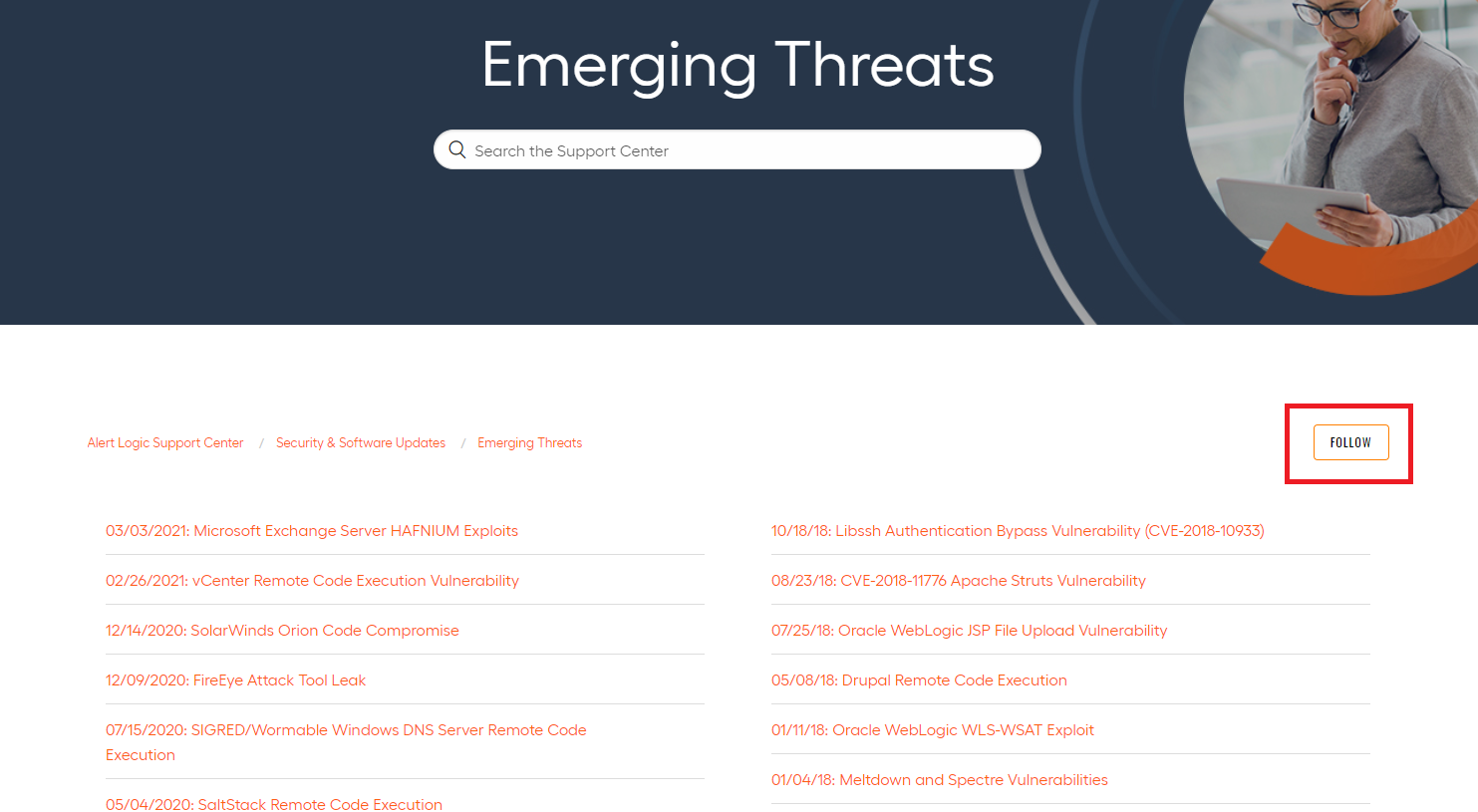
Alert Logic highly recommends following the Emerging Threat section in the Knowledge Base to stay informed of new critical vulnerabilities via email. To follow the Emerging Threat section, click the FOLLOW button on the top right corner of the section, sign in with your Alert Logic console credentials, and select New articles. By following new articles, you will receive an email any time a new Emerging Threat article is published.
If you want to stay informed of updates to a particular Emerging Threat, you can also follow the article itself by clicking the FOLLOW button within the article. By following a specific article, you will receive an update any time a comment is posted; comments are posted each time the article is updated with new information. This is the best way to keep up to date on an Emerging Threat. - Targeted Outreach
Alert Logic immediately begins assessing our customers to identify those who have been targeted by the new threat or are at risk. Outreach may occur from their designated security analyst, MDR Concierge (Customer Success Manager), email, or a combination of these depending on their subscription level.
Alert Logic will also notify our strategic partners to inform them we have initiated our Emerging Threat process and provide regular updates. - General Communication
Based on the nature of the threat, Alert Logic may send an announcement email to all customers to advise them of the Emerging Threat along with recommendations for mitigation. A recap will be included in the monthly partner newsletter and customer product updates.
Depending on the impact additional digital properties may be used, such as the alertlogic.com website, blog, and social media.
Through these various communication mediums, our goal is to keep you informed and share important steps you need to take to mitigate the vulnerability.
What if I have questions about an Emerging Threat?
The majority of questions can be answered by reviewing the Knowledge Base article for an Emerging Threat. If Alert Logic has identified that you are at risk, you will receive a communication from Alert Logic or an Alert Logic security analyst will reach out to you directly if indicators of exploitation are found.
If you have additional questions about an Emerging Threat, you can create a ticket to receive a response from the Alert Logic Support team.
Comments
0 comments
Please sign in to leave a comment.