From subscribing to Alert Logic® Cloud Insight™ Essentials to evaluating incidents from Amazon GuardDuty findings and receiving remediations to address the most important exposures first, there are steps that must be completed to deploy and provision these services. This article provides a high-level overview of the phases involved in the provisioning process.
However, detailed tutorials and additional information are available throughout the Alert Logic console. For example, the first time you access the Deployments page, a tutorial displays to describe the deployment options and process.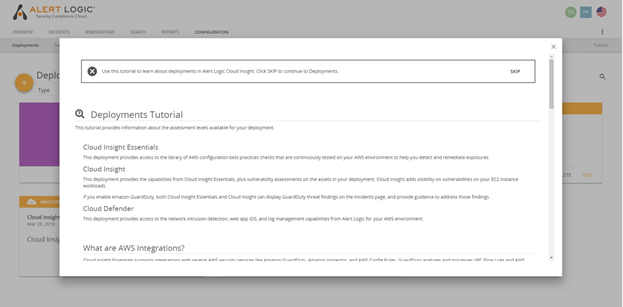
These tutorials and other detailed information can be accessed at any time in the Alert Logic console – simply look for the Information icon or the Tutorial link.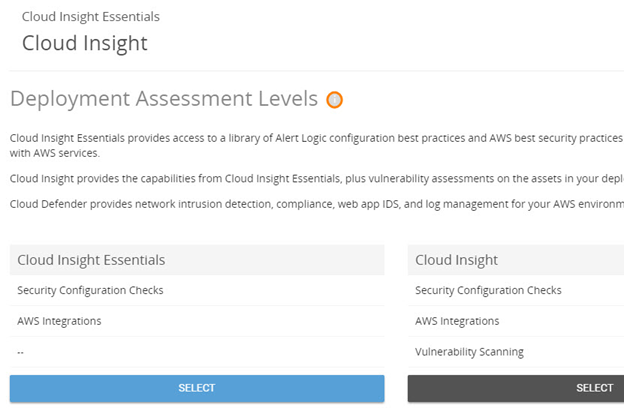
Note: The following information applies only to customers with Alert Logic® Cloud Insight Essentials™ entitlements.
Step 1 - Subscribe and Log In
After subscribing to Cloud Insight Essentials, you will receive an email that directs you to set up your account and log in for the first time into the Alert Logic console. At this point, you can start deploying Cloud Insight Essentials for your AWS account.
Step 2 - Deployment of AWS Accounts
The next step is to start deploying your AWS accounts. When deploying an account, you can choose to deploy without vulnerability scanning (Cloud Insight Essentials) or with vulnerability scanning (Cloud Insight).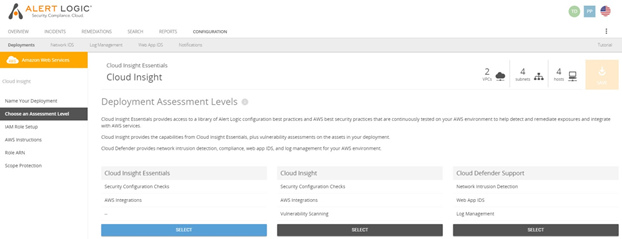
For more information about the difference between Cloud Insight Essentials and Cloud Insight, refer to the What is the difference between Cloud Insight and Cloud Insight Essentials? knowledge base article. While the steps remain largely the same, this article assumes a deployment without vulnerability scanning.
Note: If you choose to deploy with vulnerability scanning, additional charges will be incurred.
Alert Logic provides a policy to create a role to allow Alert Logic permission to access your AWS account.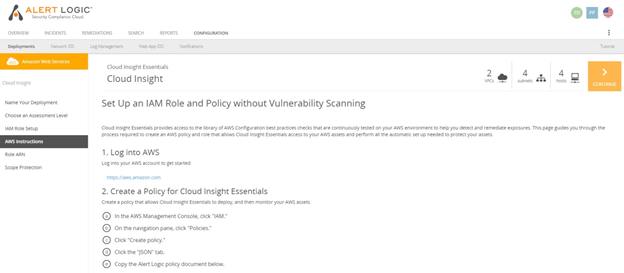
This policy allows Cloud Insight Essentials to discover your deployment, perform configuration checks, and integrate Amazon GuardDuty data for display on the Incidents page.
Note: If you choose to deploy with vulnerability scanning, a different role and additional permissions are needed for Cloud Insight. For more information, refer to the What kind of additional roles and permissions are needed for vulnerability scanning? knowledge base article.
Once these actions have been performed in your AWS account and completed in the Alert Logic console, Alert Logic will begin the discovery phase.
Step 3 - Discovery
After you create your deployment for the AWS account you want to monitor, Cloud Insight Essentials accesses the account and discovers the regions, VPCs, and subnets associated with the account. The discovery processes may take some time to complete.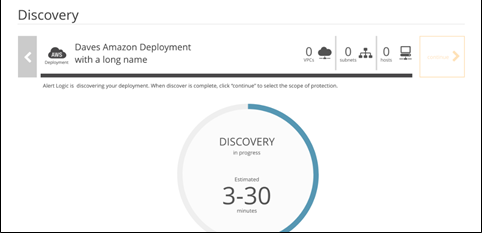
Once the discovery process is complete, you are presented with options to select your deployment scope.
Step 4 - Select Your Scope
After discovery, you must select the regions and VPCs you want to monitor. You can choose to monitor the full scope, or specify only certain VPCs or subnets for which you want to receive incident information and recommendations.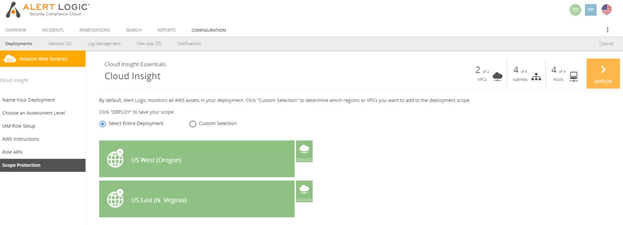
Remediations are provided only for your selected scope.
Step 5 - Review Remediations
After selecting your scope, you can access the Remediations Dashboard to review the remediation actions that have been generated for your deployment.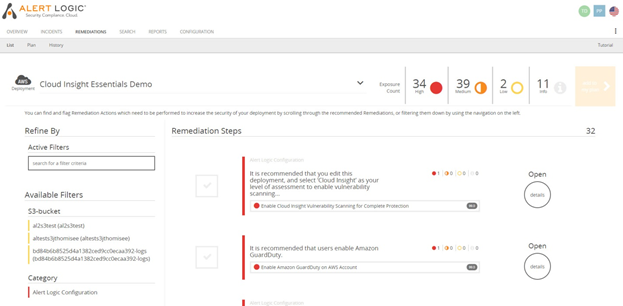
Cloud Insight lists the recommended actions to remediate exposures for the selected deployment. Remediations include:
- Exposures discovered after a configuration check.
- Services you should enable, which could involve additional provisioning steps.
- Configure the product to connect to new data sources, such as Amazon GuardDuty.
These remediations are prioritized to help you focus on the most recommended remediations first, such as enabling GuardDuty and installing the Alert Logic collector for GuardDuty findings.
Step 6 - Enable Amazon GuardDuty
If you have not already enabled GuardDuty, you can start the process by adding this action to your remediation plan and following the process provided for the remediation.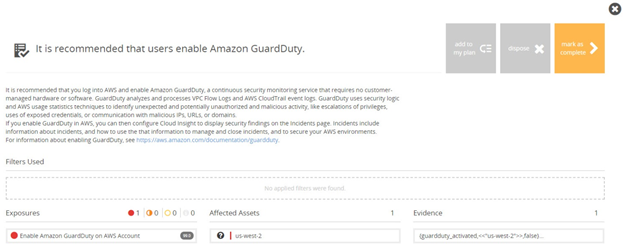
Additional information about enabling GuardDuty is available in Amazon’s GuardDuty user guide.
Once GuardDuty is enabled, complete the related remediation action to install Cloud Insight collectors for GuardDuty. The collector is installed using a CloudFormation template. Once these two items are complete, Cloud Insight Essentials can start ingesting GuardDuty findings and generating remediation actions based on incidents found by GuardDuty.
These steps complete the provisioning process for Cloud Insight Essentials and Amazon GuardDuty. After deployment, you can utilize the reporting tools available, such as the Incident Daily Digest, to help you in your day-to-day monitoring and remediation efforts.
Still have questions? Check out other customers’ posts or add your own in the Cloud Insight Essentials community.
Comments
0 comments
Please sign in to leave a comment.