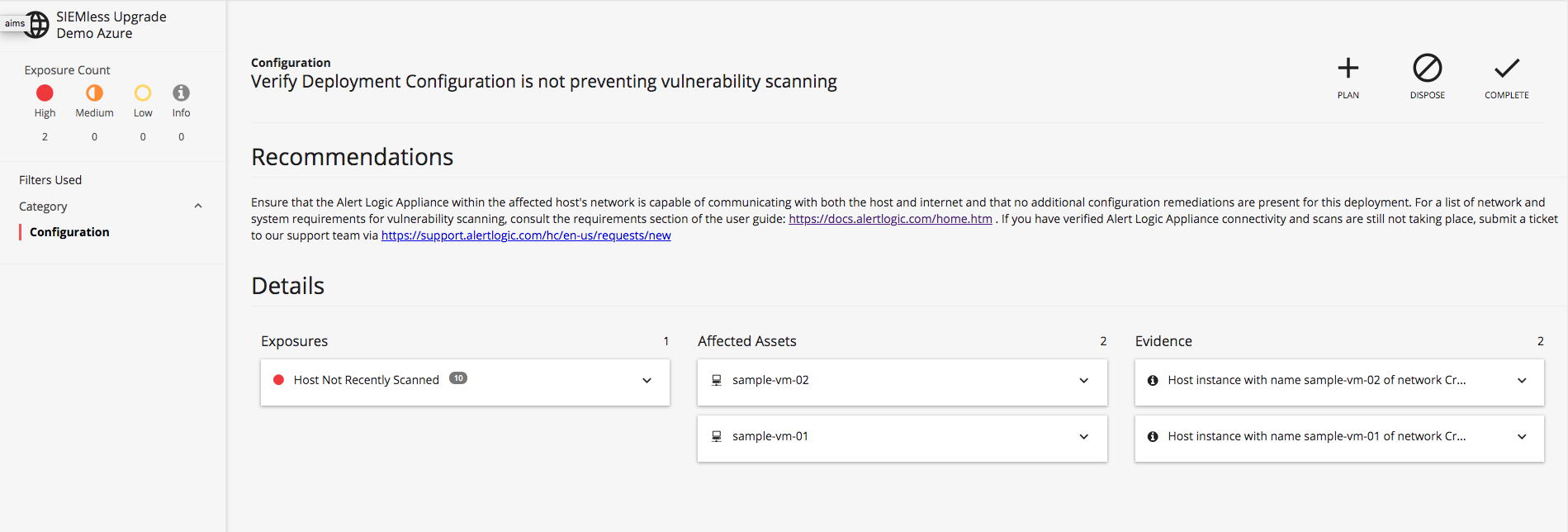
Alert Logic® customers who have deployed and enabled vulnerability scanning in their environments may see the following health remediation, "Verify deployment configuration is not preventing vulnerability scanning," within the Alert Logic console. Alert Logic Managed Detection & Response (MDR) customers can find remediations at navigation menu (![]() ) > Respond > Health > Unhealthy > View drop-down > Exposures.
) > Respond > Health > Unhealthy > View drop-down > Exposures.
This remediation indicates that vulnerability scans are not taking place within the scanning window that you configured when setting up your deployment.
Note: Amazon Web Services (AWS) hosts with whitelisted tags attached are exempt from these scans and will not have a remediation generated.
Utilize the following steps to identify the cause of and remediate your vulnerability scanning failure.
Solution
1. Verify Appliance-to-Host Connectivity
A common reason that vulnerability scans fail is due to connectivity issues between your Alert Logic appliance and protected host subnets.
Symptoms
- Vulnerability scans are repeatedly failing for certain hosts
- Vulnerability scans are repeatedly failing for all hosts in a given network
To verify that appliances are able to reach protected hosts, review scanning connectivity requirements and ensure your infrastructure allows access to the required ports:
If you are using cross-network protection across your networks and deployments, you will also need to verify that your protecting networks can reach their associated protected networks. Review the full list of connectivity requirements for cross-network protection in our Cross-Network Protection Scanning Requirements documentation.
AWS Deployments
For AWS deployments, Alert Logic can detect standard networking configurations that would prevent scans from taking place. A relevant remediation is generated with details on what specific part of your network is blocking vulnerability scans. Issues that are detected on AWS deployments by Alert Logic include:
- Security groups blocking required ports
- Network Access Control Lists blocking required ports
2. Verify Appliance-to-Internet Connectivity
The Alert Logic appliance can only report vulnerability scan results if it has access to Alert Logic via the public internet, so you will need to confirm that your appliance is connected to the internet.
Symptoms
- Vulnerability scans are repeatedly failing for hosts in the appliance's network
- Vulnerability scans are repeatedly failing for hosts in the associated protected network
To ensure your Alert Logic appliance is capable of reaching Alert Logic, confirm that the appliance's subnet is capable of routing traffic to the public internet. Review the scanning connectivity requirements and ensure your infrastructure allows access to the required ports:
AWS Deployments
For AWS deployments, Alert Logic can detect standard networking configurations that would prevent appliances from reaching Alert Logic. A relevant remediation is generated with the details on what specific part of your network is blocking vulnerability scans. Issues that are detected on AWS deployments by Alert Logic include:
- No default route to an Internet Gateway present in associated subnet's route table
However, if you make use of NAT gateways or route via one of your hosts, Alert Logic is unable to detect routing misconfigurations, and you will be required to confirm internet access is possible manually from the appliance's subnet. Utilize the AWS documentation to complete this requirement.
3. Verify Appliance Is Not Overloaded
Vulnerability scans can fail due to the appliance being unable to scan all its assigned hosts as frequently as configured by the deployment.
Symptoms
- Constant scanning activity
Note: For Automatic scanning deployments, this will be further evidenced by the appliance never scaling down.
There are several solutions to address this issue:
a) Decrease Frequency of Vulnerability Scans
Decrease the load on the appliance by changing the frequency of vulnerability scans of the affected deployment. In the Alert Logic console, navigate to navigation menu () > Configure > Deployments > select a deployment > Scan Schedules. Click the Add (
) icon to create a new scan schedule or select an existing scan schedule to edit.
b) Increase the Number of Appliances
To maintain the current scan frequency, reduce the load on the appliance by deploying additional appliances into the affected network.
- Manual mode deployments - Provision an additional appliance in your platform. Installation details are available for the following platforms:
- Automatic mode deployments - Configure load balance via the OTIS API in our API documentation
4. Check the Alert Logic Status Page
In some cases, there may be issues on the Alert Logic side due to maintenance or outages. Check the status of the Alert Logic services by reviewing the Alert Logic status page.
5. Contact Alert Logic Support
If your issue persists after verifying the appliance is connected to the host, verifying the appliance is connected to the internet, verifying the appliance is not overloaded, and checking the Alert Logic status page, submit a ticket with Alert Logic Support. Reference the affected deployments and your remediation steps.
Comments
0 comments
Please sign in to leave a comment.