This article describes how to find assets, such as computers, services, and EC2 workloads, that are vulnerable to a specific CVE. This information can be retrieved from the Alert Logic console – you can quickly review the affected assets and related mitigation steps through the Exposures page.
Solution
- In the Alert Logic console, navigate to the Exposures page by selecting
 (navigation menu) > Respond > Exposures.
(navigation menu) > Respond > Exposures. - Open the drop-down menu at the top of the data table that reads Remediations and select Exposures.
- Enter a specific CVE or text string in the Search bar at the top right of the data table.
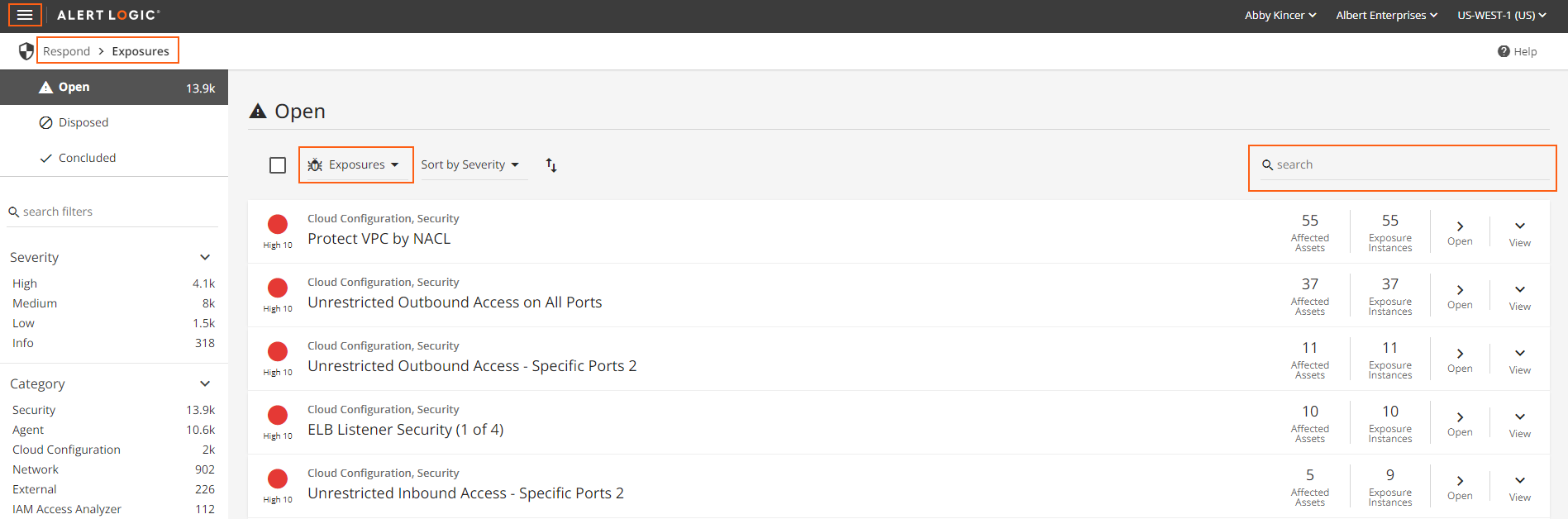
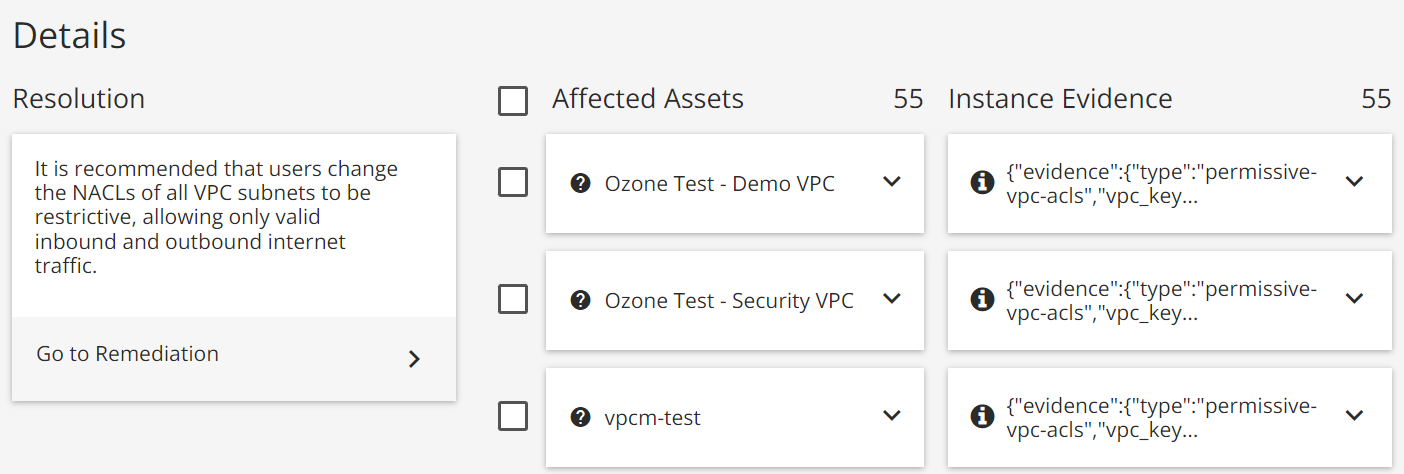
- Click Open to view the affected assets and remediation steps.
Additional Resources
Learn how to export a list from the Alert Logic console with our Export a List of Hosts Affected by a Specific Vulnerability, Remediation, or Exposure knowledge base article.
Comments
0 comments
Please sign in to leave a comment.