The Configure group, found in the navigation menu (![]() ), houses the following pages:
), houses the following pages:
Deployments
The Deployments page houses all your deployments and is color-coded based on deployment type:
Add a new deployment via the add icon (![]() ), or click on any deployment tile to edit its settings.
), or click on any deployment tile to edit its settings.
Data Center Deployments
When you click into a data center deployment, the following menu items are available -
Assets
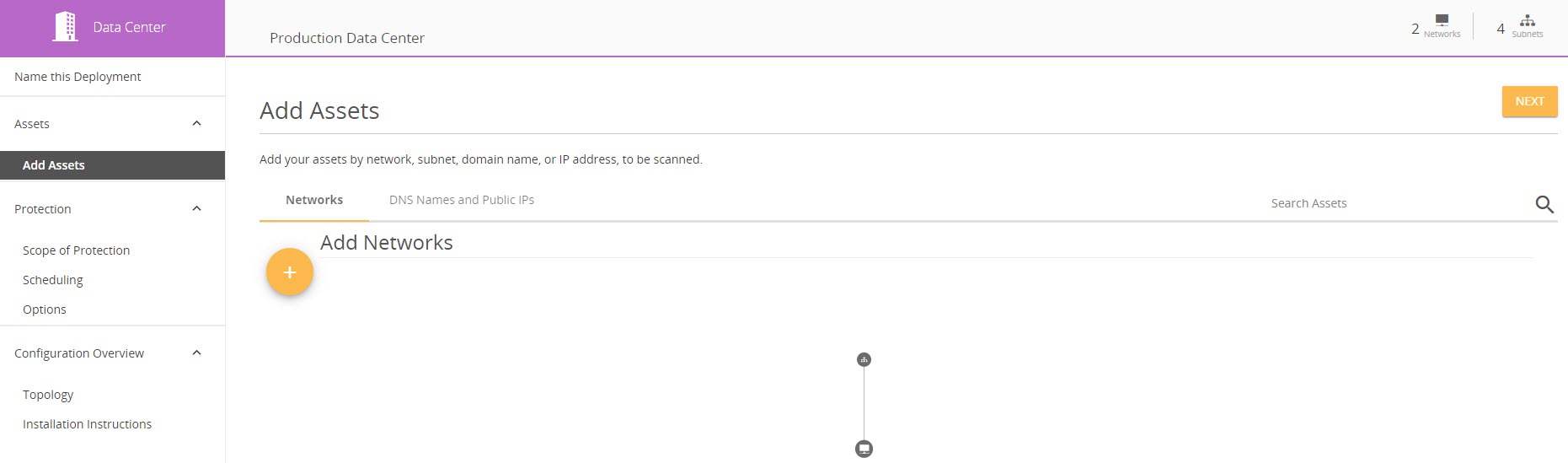
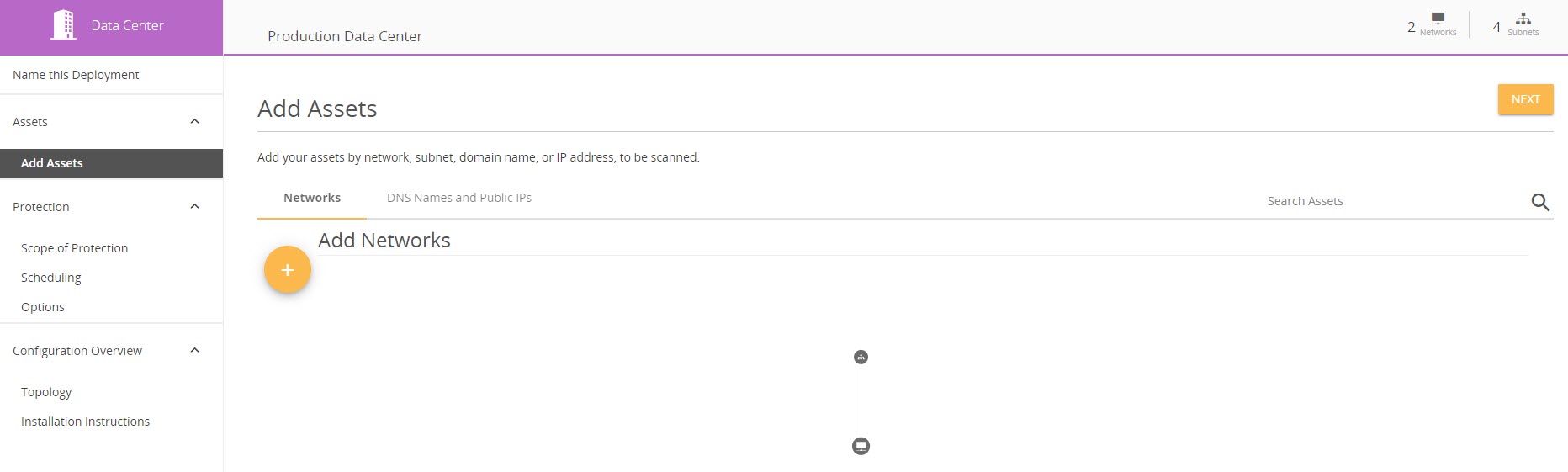
Add Assets
On the Add Assets tab, you can add your assets by network, subnet, domain name, or IP address, to be scanned. You can also view the topology of your networks and subnets and edit or delete them by clicking on the applicable network or subnet icon. Further, you can edit DNS names and search all assets.
Protection
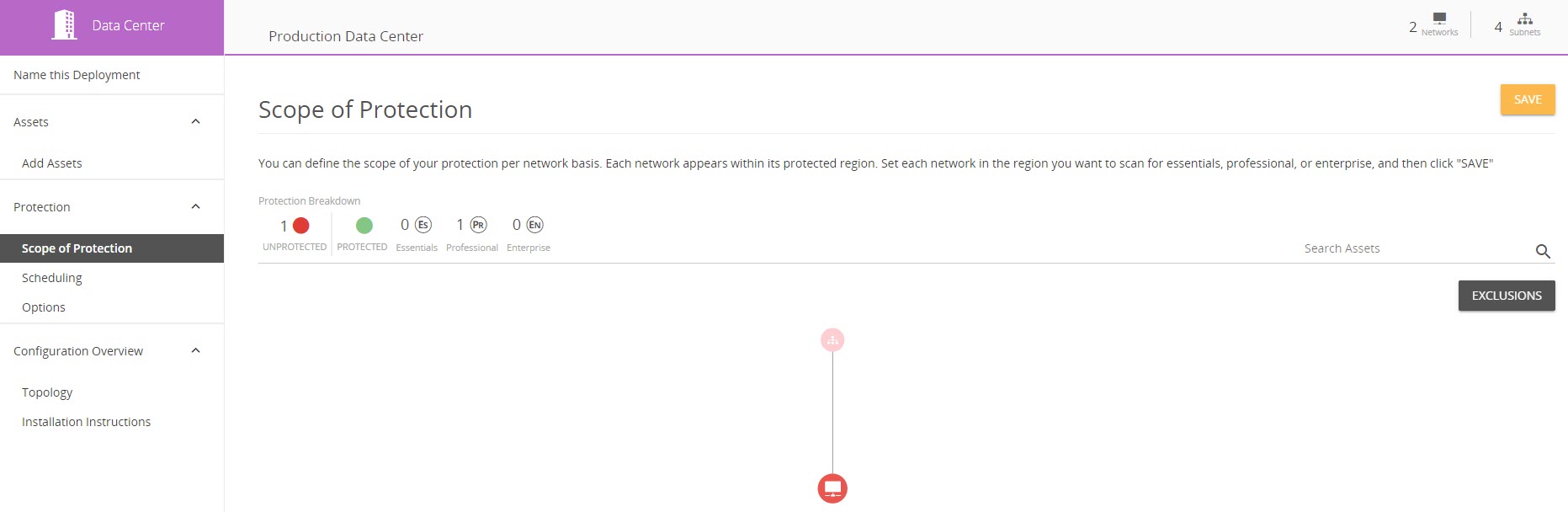
Scope of Protection
The Scope of Protection tab allows you to define the scope of your protection for each asset in your deployment. Each asset appears within its protected region. Set each asset in the region you want to scan for Alert Logic® Essentials or Professional and click Save.
Manage exclusions for the deployment - including external scanning, internal scanning, and network intrusion detection scanning whitelist - by clicking Exclusions.
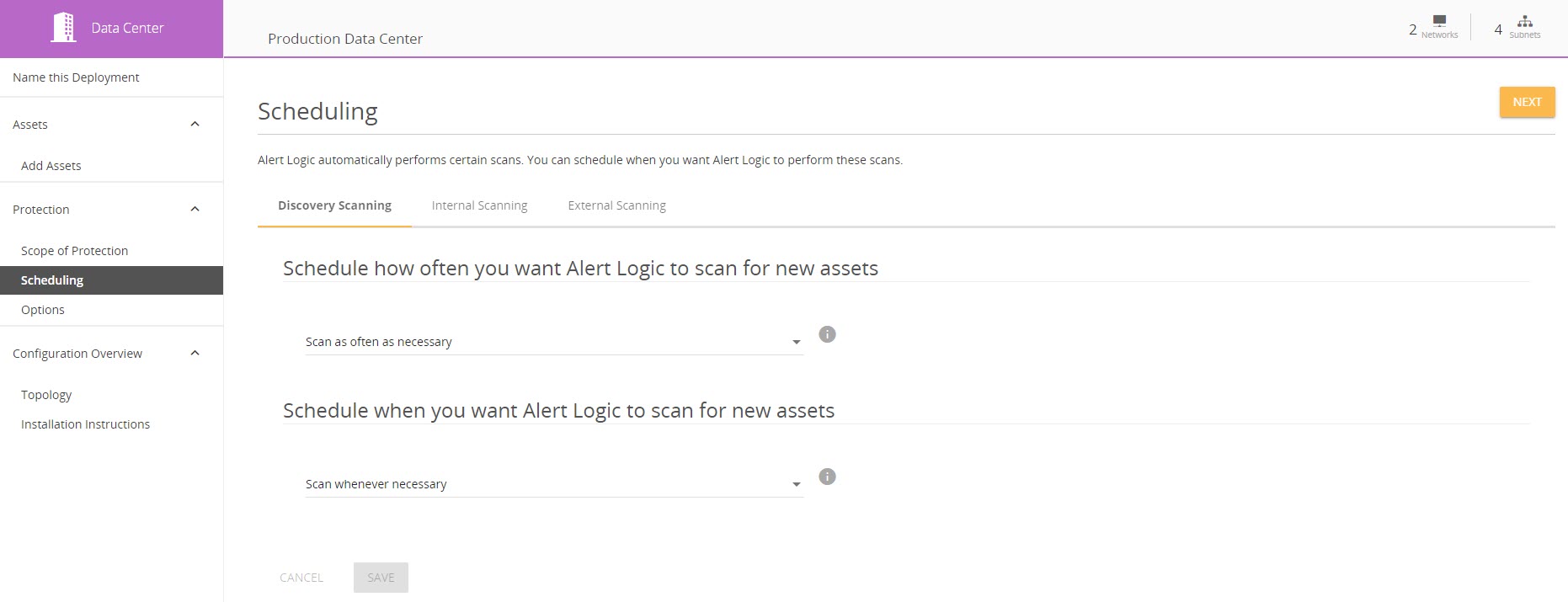
Scheduling
Alert Logic automatically performs certain scans. You can schedule when you want Alert Logic to perform these scans on the Scheduling tab.
Learn more about scan scheduling in Manage Scan Schedules.
Options
The Options tab houses a topology of your networks and subnets, as well as the capability to create and manage cross-network protections.
Here, you can configure a network configured with an appliance to provide protection to other networks under the same Alert Logic console account with agents installed. For more information on cross-network protection, see the Cross-Network Protection knowledge base article.
Configuration Overview
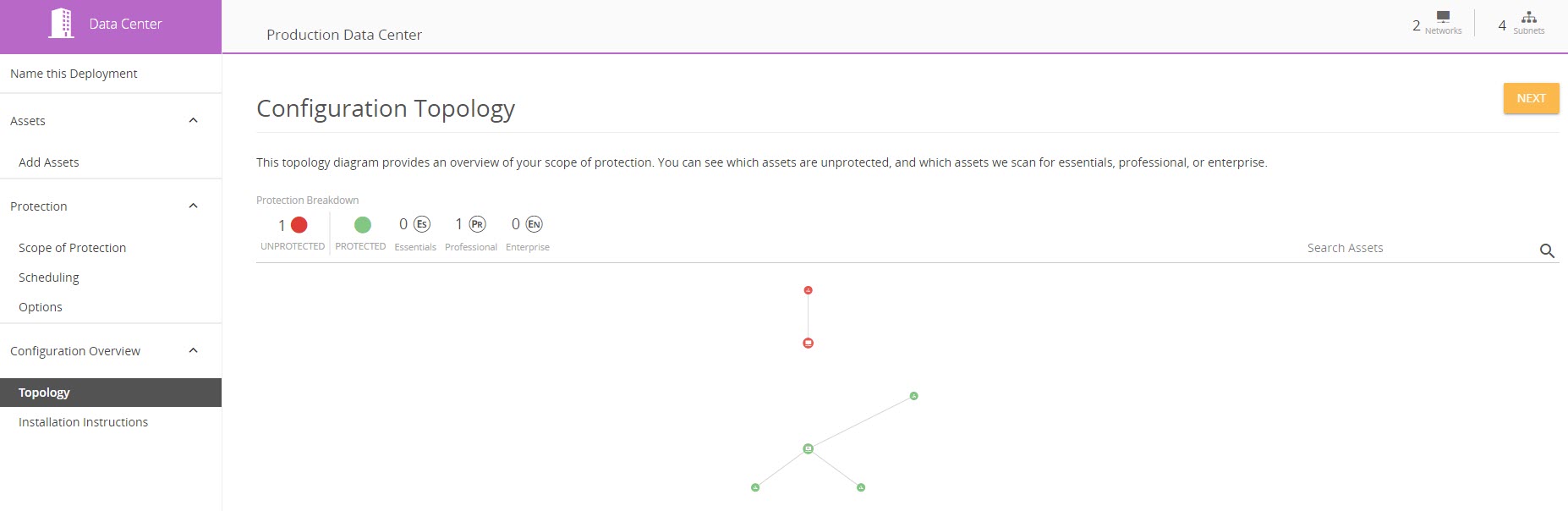
Topology
The Topology tab houses a topology diagram that provides an overview of your scope of protection. You can see which assets are unprotected, as well as which assets we scan for Essentials, Professional, or Enterprise.
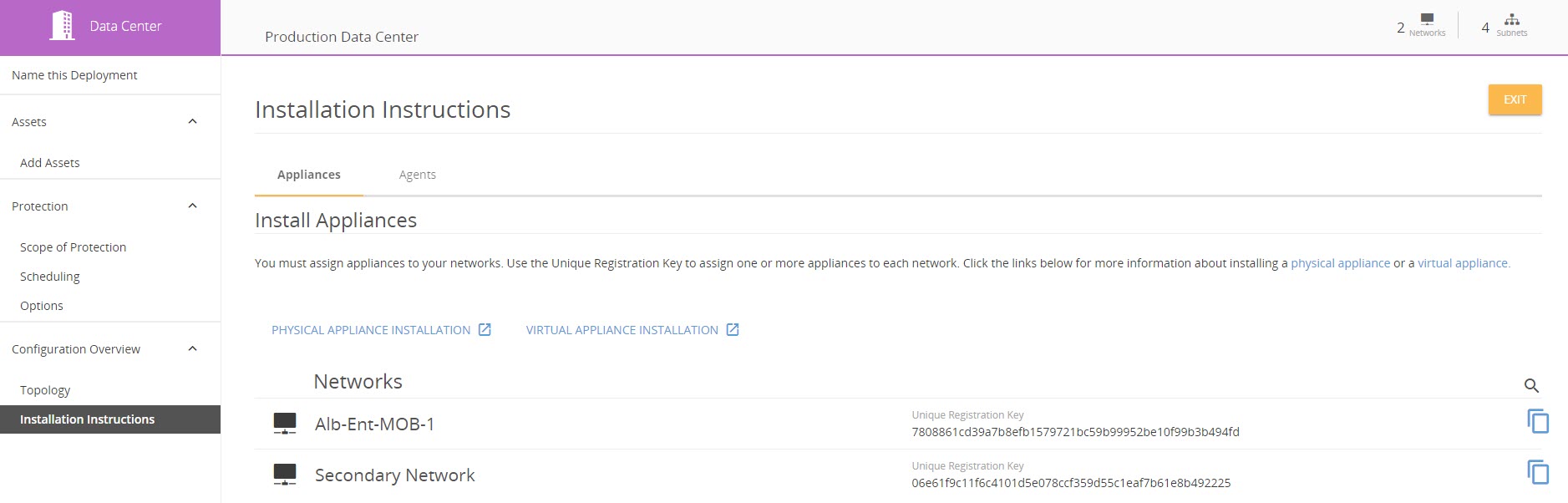
Installation Instructions
The Installation Instructions tab houses instructions on installing appliances and agents, as well as network Unique Registration Keys.
Amazon Web Services Deployments
When you click into an Amazon Web Services (AWS) deployment, the following menu items are available.
Access to AWS Account
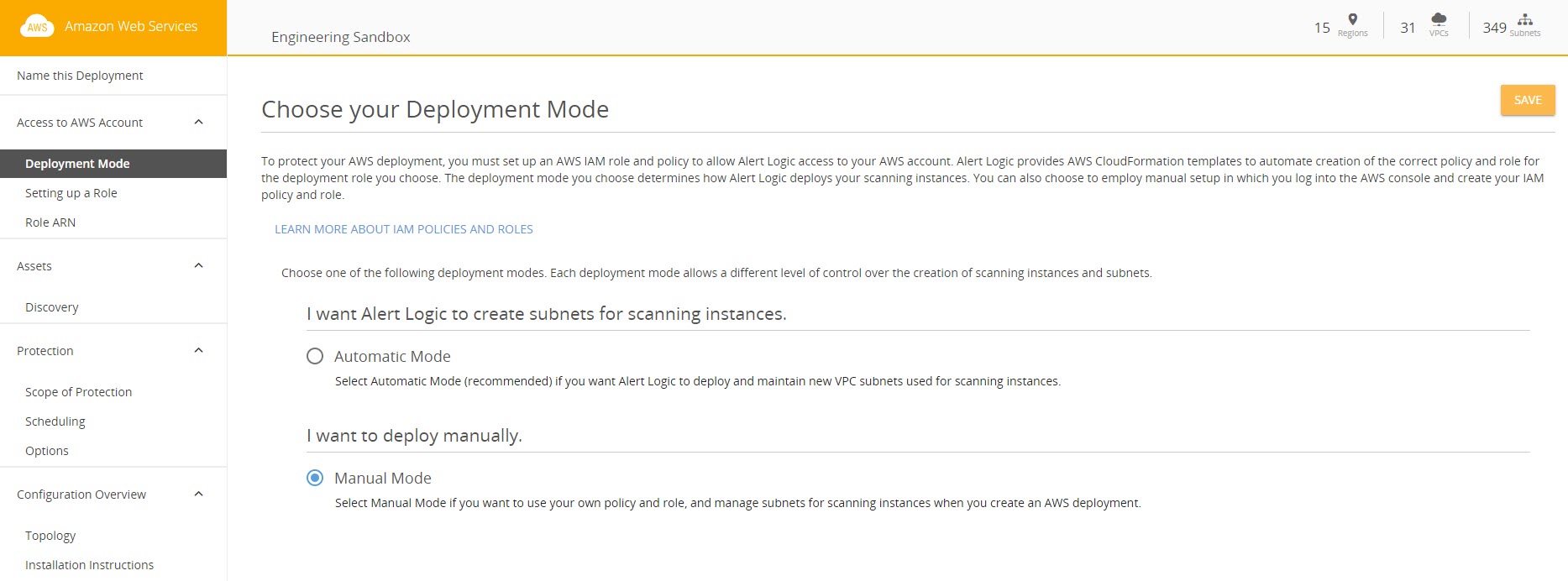
Deployment Mode
To protect your AWS deployments, you must set up an AWS IAM role and policy to allow Alert Logic access to your AWS account. The Deployment Mode tab houses the two deployment modes that you can choose from:
- Automatic - Alert Logic will deploy and maintain new VPC subnets used for scanning instances
- Manual - Use your own policy and role and manage subnets for scanning instances when you create an AWS deployment
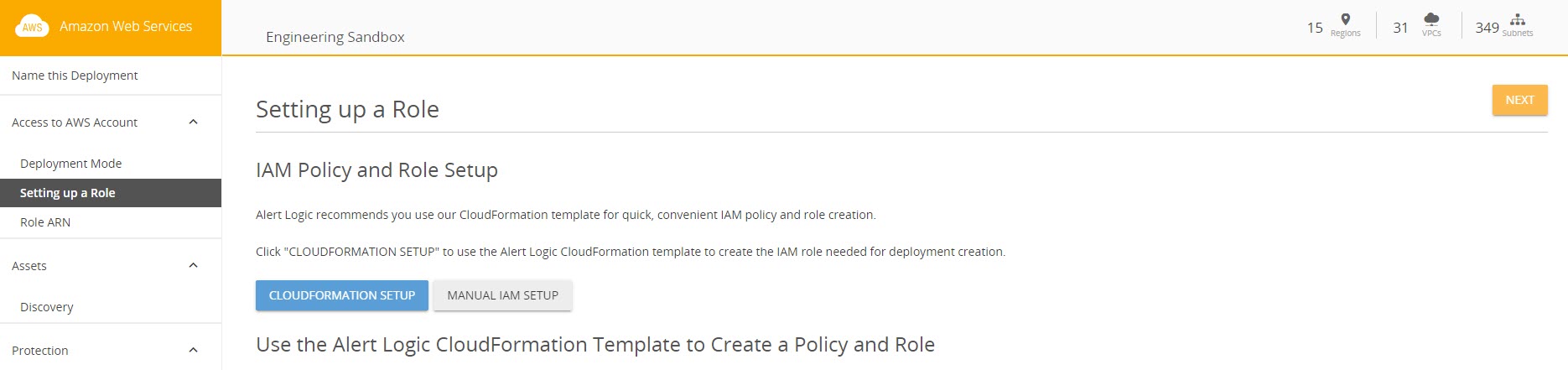
Setting Up a Role
The Setting Up a Role tab houses your IAM policy and role setup and instructions. Alert Logic offers two options to set up your IAM role - CloudFormation or manual.
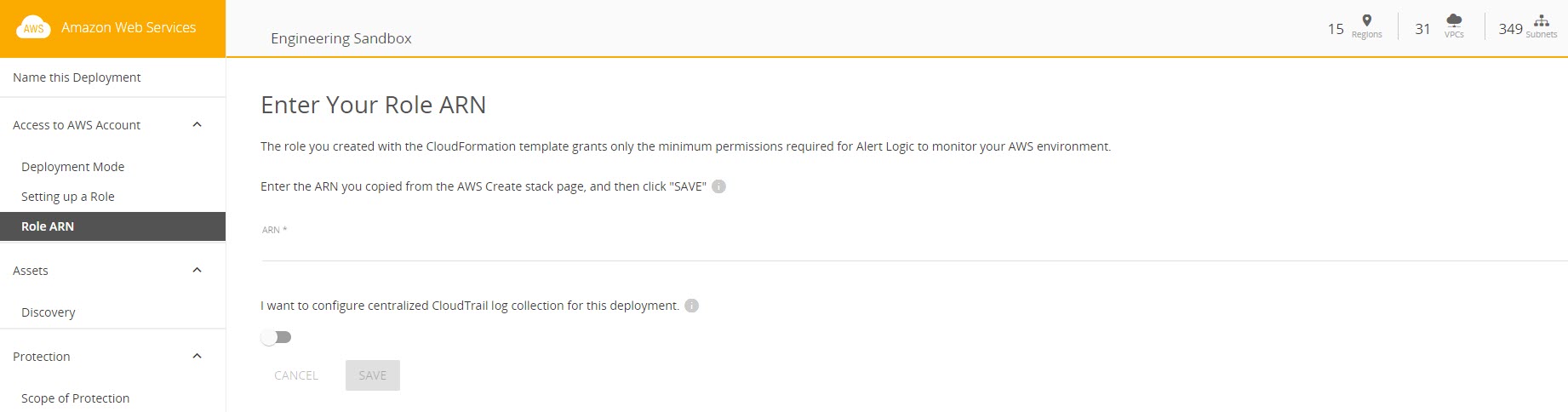
Role ARN
The IAM policy and role that you previously created allow Alert Logic to access your AWS account. Entering a role ARN at the Role ARN tab will provide Alert Logic permissions to monitor your AWS environments.
Assets
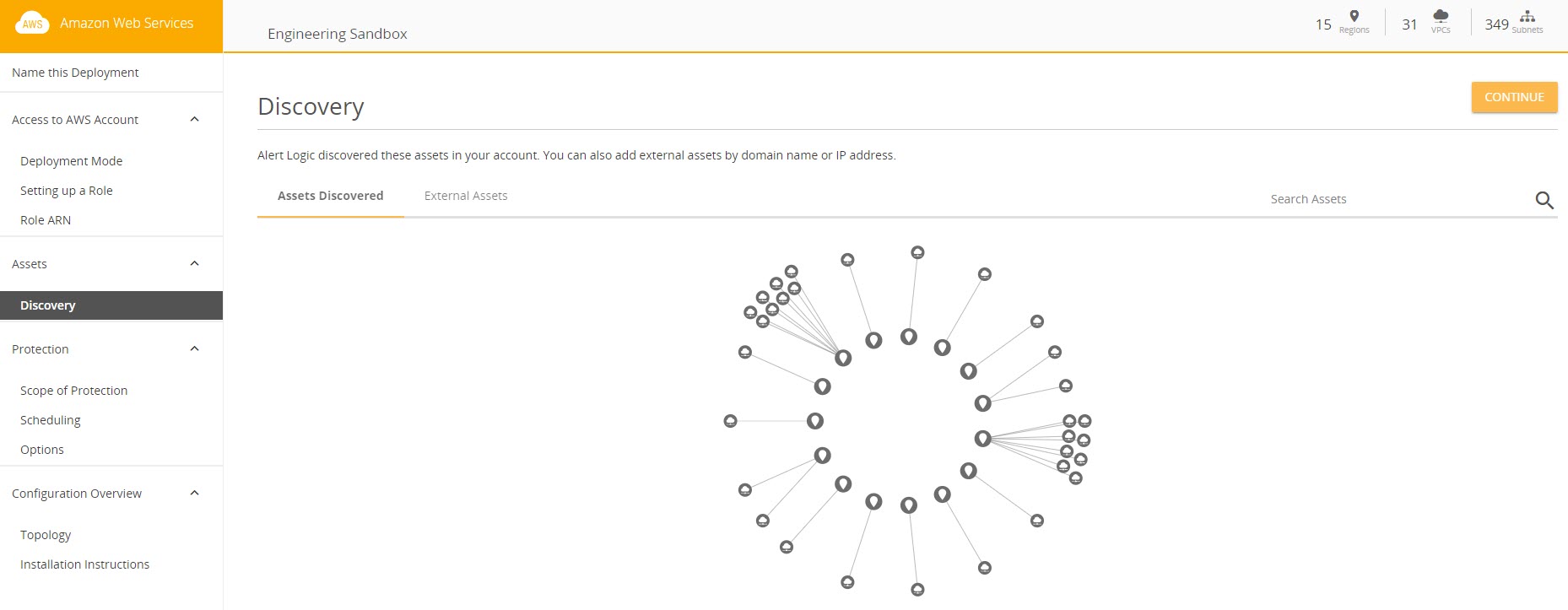
Discovery
The Discovery tab houses a topology diagram of all the assets discovered by Alert Logic on your AWS account. You can add external assets within the External Assets tab.
Protection
The Protection group is the same for AWS deployments as for data center deployments. See the Protection section above for more information.
Configuration Overview
The Configuration Overview group is the same for AWS deployments as for data center deployments. See the Configuration Overview section above for more information.
Microsoft Azure Deployments
When you click into a Microsoft Azure deployment, the following menu items are available -
Access to Azure Subscription
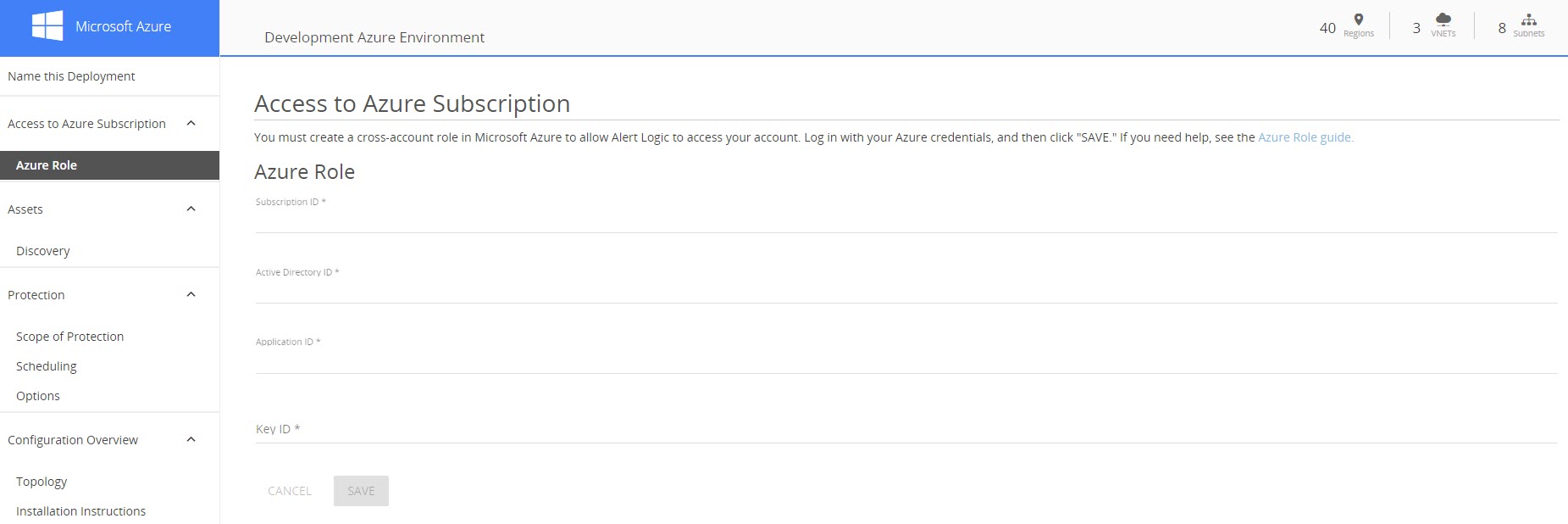
Azure Role
The Azure Role tab houses instructions for creating cross-account roles in Microsoft Azure to allow Alert Logic to access your account, as well as important Azure Role IDs.
Assets
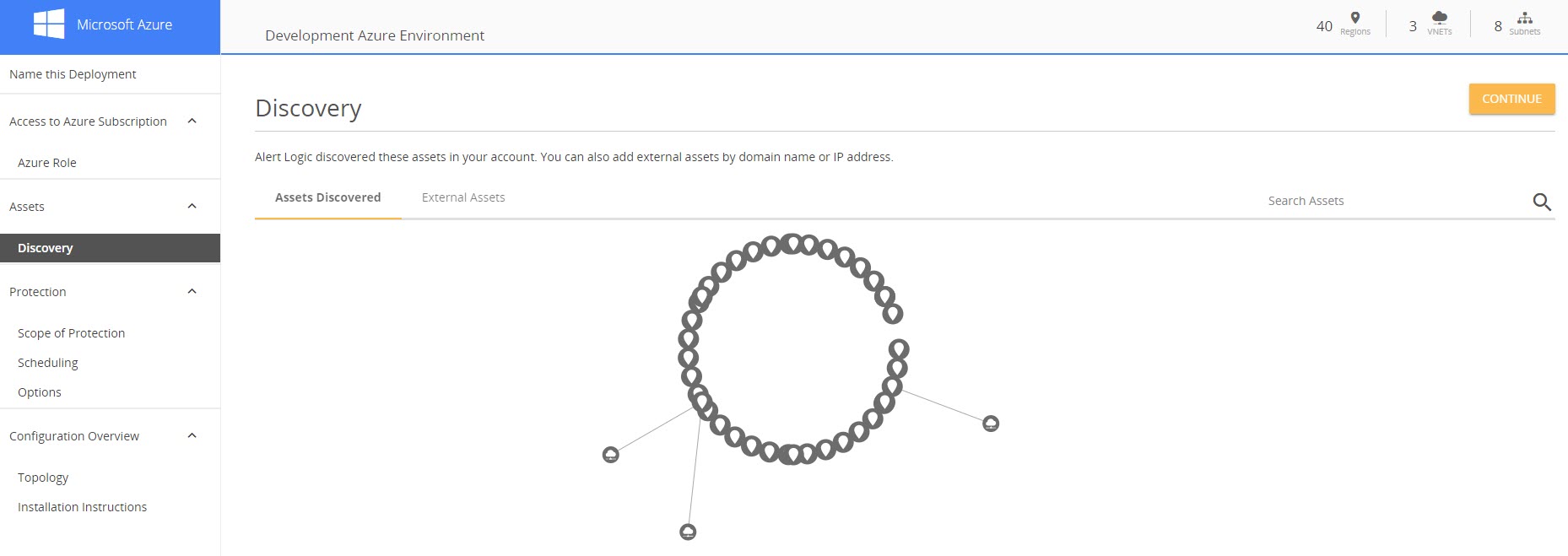
Discovery
The Discovery page houses a topology diagram of all the assets discovered by Alert Logic on your Azure account. You can add external assets within the External Assets tab.
Protection
The Protection group is the same for Azure deployments as for data center deployments. See the Protection section above for more information.
Configuration Overview
The Configuration Overview group is the same for Azure deployments as for data center deployments. See the Configuration Overview section above for more information.
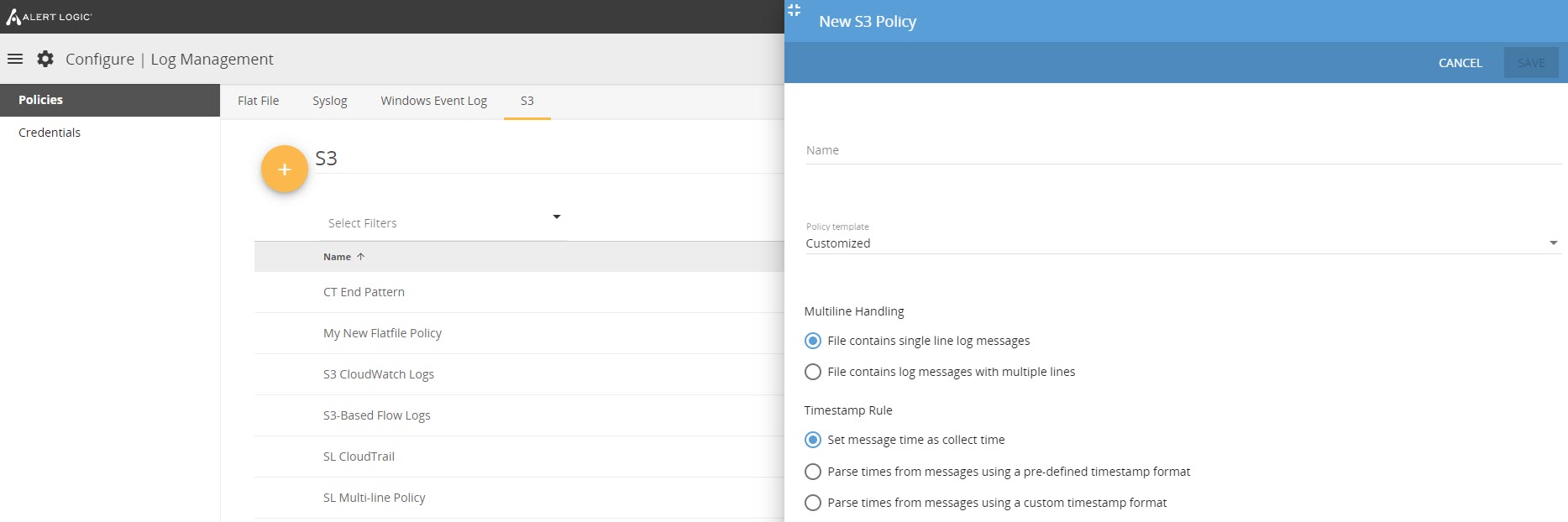
Log Management
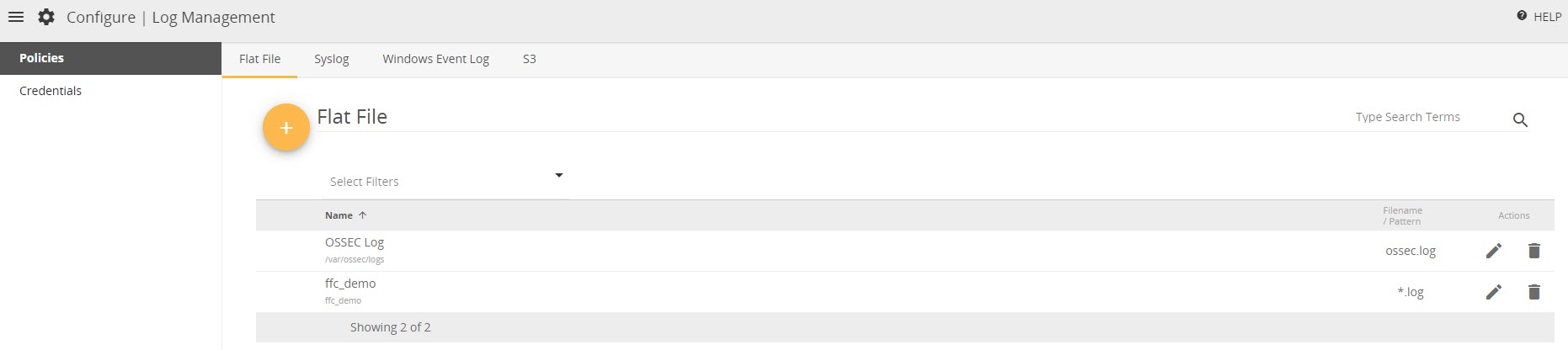
The Log Management page provides access to configuration of log management policies - flat file, syslog, Windows Event Log, and S3 - and credentials. Navigate between the Policies and Credentials tabs to manage - add, edit, or delete - these components of your Log Management entitlement.
Policies
Flat File
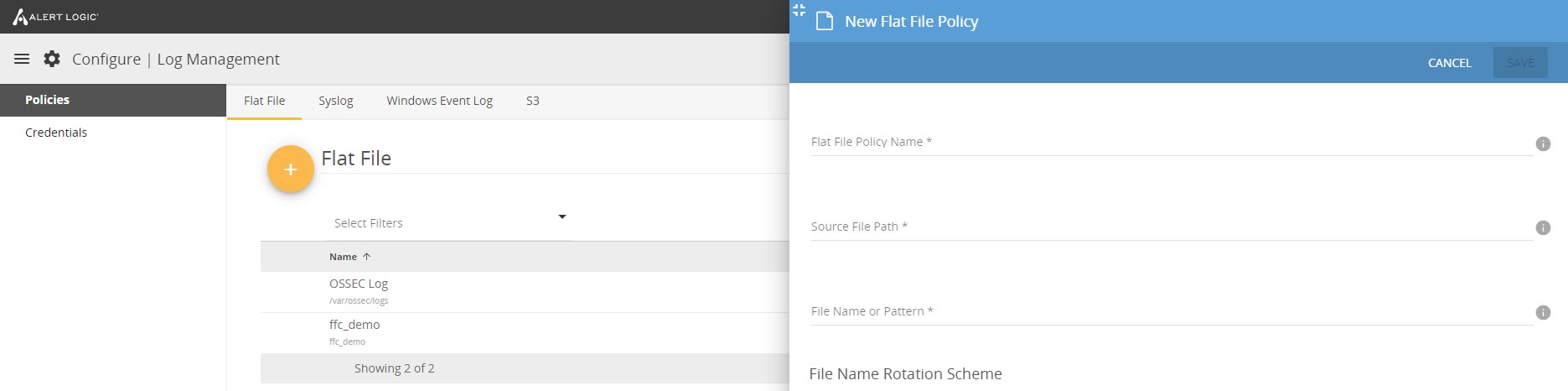
Flat File log messages - also known as text-based - are a common format and can be collected, stored, and normalized. A flat file policy specifies where the log file is located and tells Alert Logic how to read the file, which allows for the message to be received and parsed correctly.
Learn more about flat file policies with our Flat File Correlation Policy documentation.
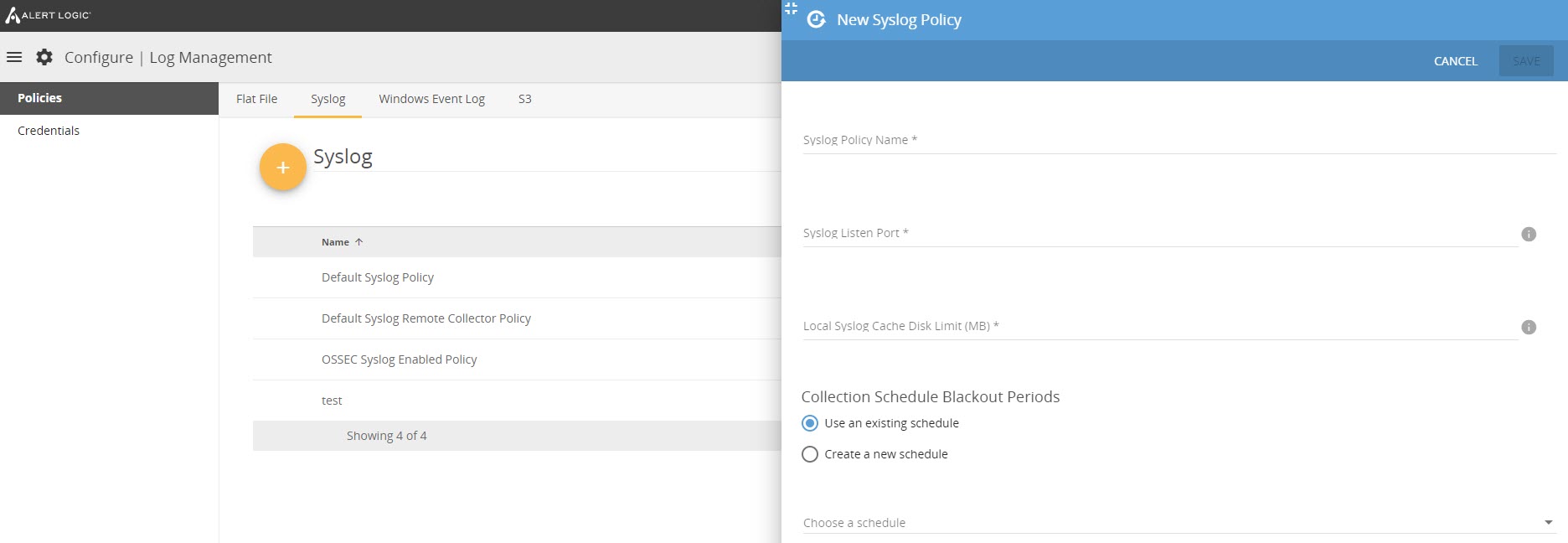
Syslog
Syslog is a way for network devices to send event messages to a logging server (often known as a syslog server). A syslog policy lets you collect syslog files for Alert Logic Log Management to review. Syslog policies are used for defining the port that is listening for syslog traffic in both the agent and remote collector. The policy is also used for defining how much data can be cashed on the agent or collector if the connection to the Alert Logic cloud is lost, or if there is insufficient bandwidth for transmitting the received logs.
Learn more about syslog policies with our Syslog Collection Policy documentation.
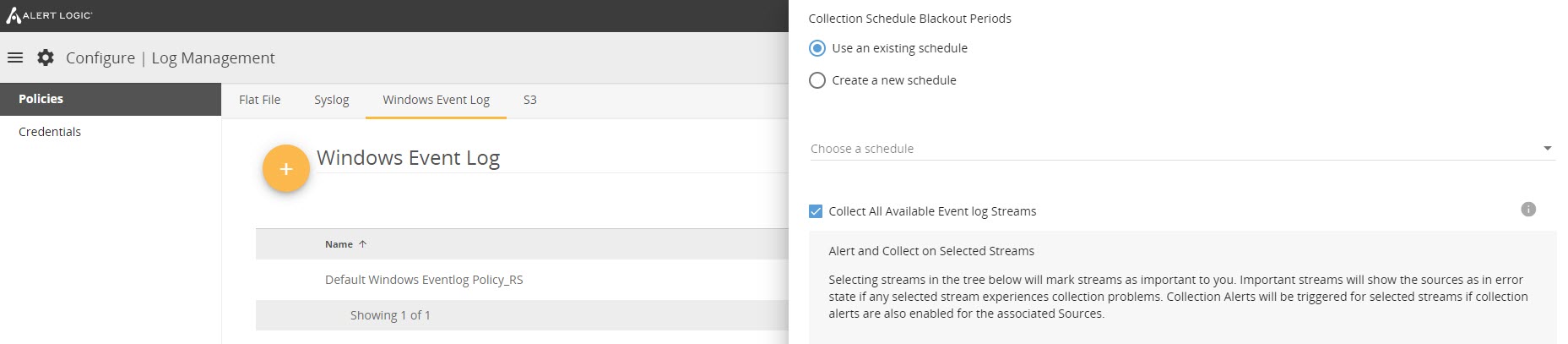
Windows Event Log
Windows Event Log files track significant events on a Windows server, such as a user login or program error. A Windows Event Log policy lets you collection Event Log files for Alert Logic Log Management to review. Event Log policies are used for determining what Event Log streams are collected on Windows hosts. Be default, Application, Security, and System are collected.
Windows Event Log policies can be used to specify the credentials if it is not using an agent and collection scheduled is used on the source. When configuring the Windows Event Log policy using these procedures, you can filter the Event Logs you want to send by selecting the desired streams under Alert and Collect on Selected Streams. This process can help prevent receiving unwanted logs in your email.
Learn more about Windows Event Log policies in the Windows Event Log Policy documentation.
S3
S3 collection policies set guidelines for collecting amazon Simple Storage Service (S3) access logs, which provide details about a single access request, such as the requester, bucket name, request time, request action, response status, and any error codes. An S3 policy lets you collect S3 logs for Alert Logic Log Management to review.
Note: Although this feature appears to all users, only AWS accounts can set these policies.
Learn more about S3 policies with our S3 Collection Policies and Log Manager for AWS S3 documentation.
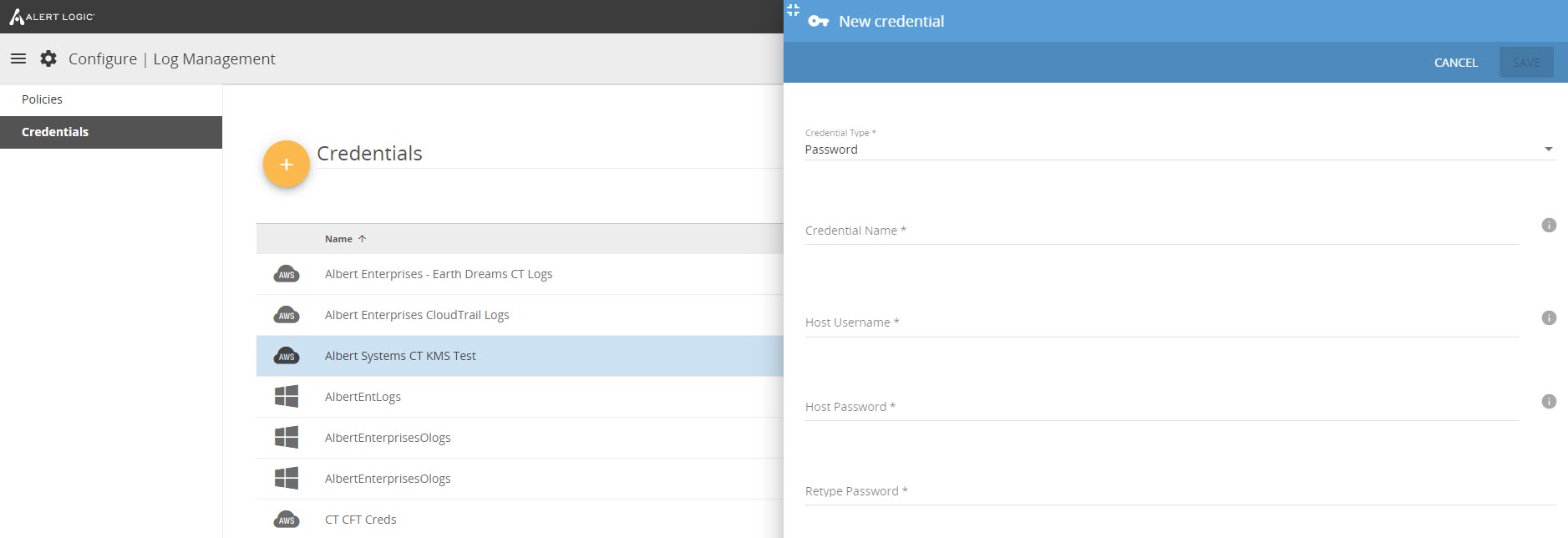
Credentials
A Credential is the information required for Alert Logic Log Management to authenticate itself to a log source in order to collect log data. The following types of credentials are stored and manageable on the Credentials page:
- Windows passwords - used for agentless Windows log collection
- IAM roles - used for S3 bucket and CloudTrail log collection
- Azure - used for Azure-based log collection
You can create, edit, and delete credentials on this page, but you can also create them during log source creation. Credentials are only used for cloud-native collection and remote (appliance-based) Windows Event Log and remote flat file collection.
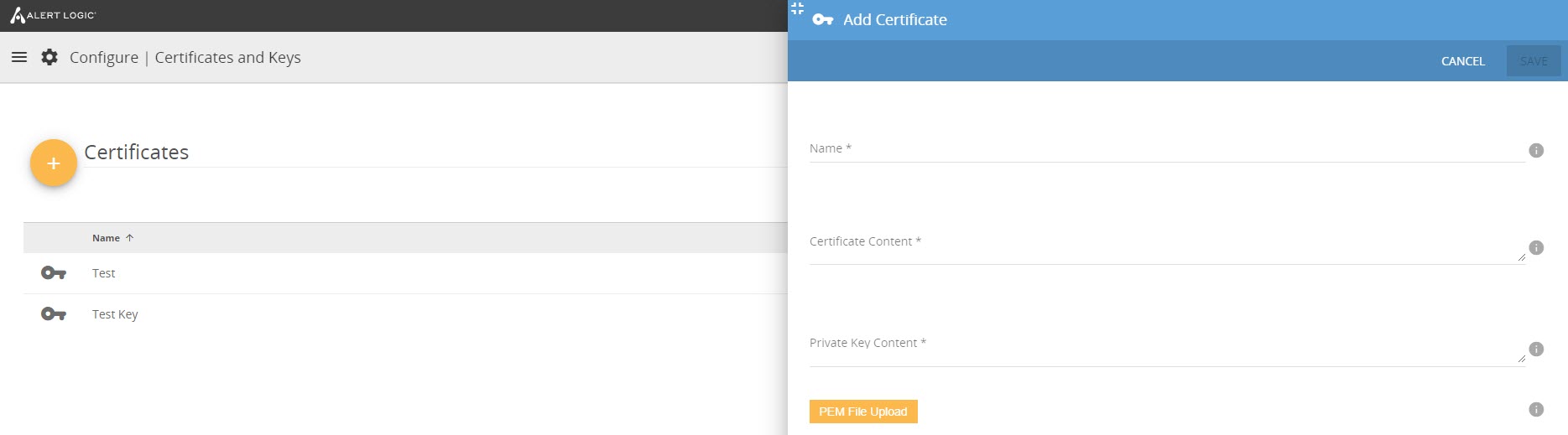
Certificates and Keys
The Certificates and Keys page allows you to manage - add, edit, and delete - your deployment's security certificates.
Learn more about certificates and keys with our Certificates documentation.
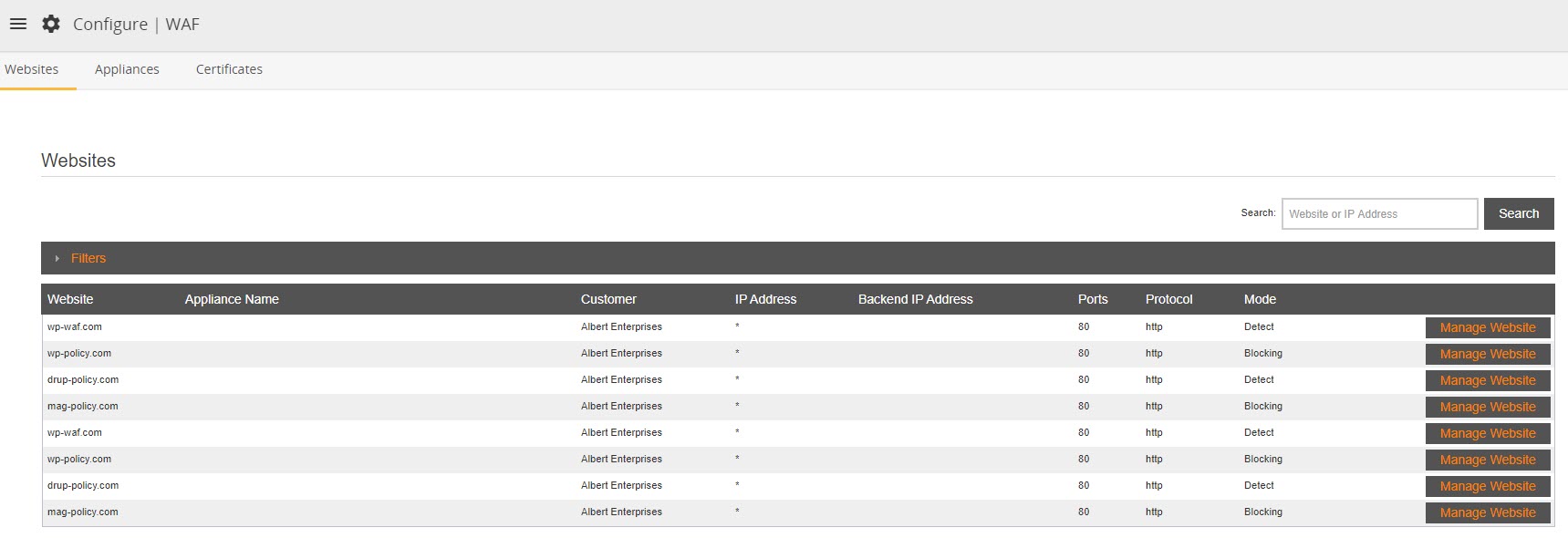
WAF
The WAF page provides access to configuration of web application firewall (WAF) websites, appliances, and certificates. Navigate between the Websites, Appliances, and Certificates tabs to manage these components of your WAF entitlement.
Endpoints
The Endpoints page houses the following resources:
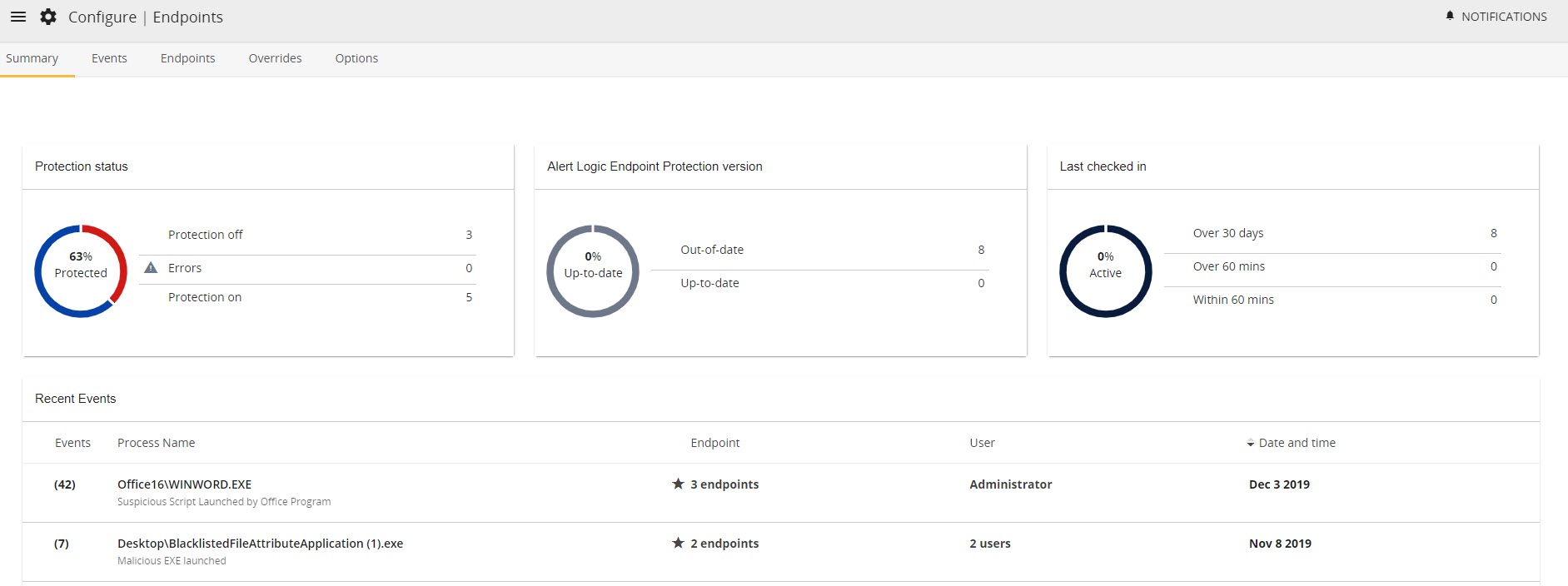
Summary
The Summary tab provides a high-level overview of the endpoints in your environment. Interactive graphs are available for information including Protection status, Alert Logic Endpoint protection version, and Last checked in, and a detailed table lists all Recent Events.
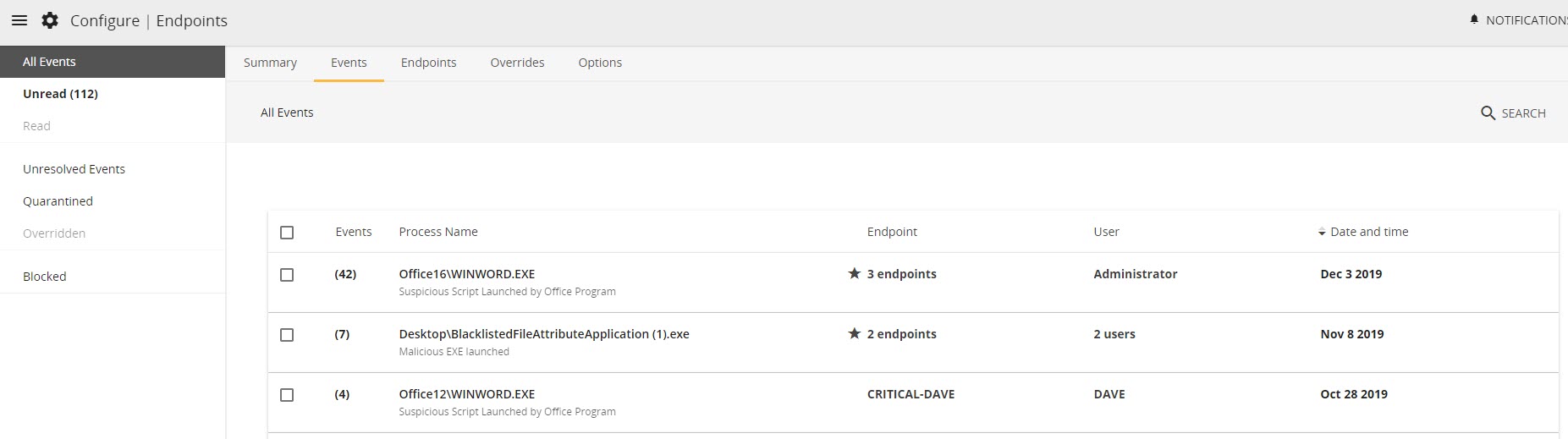
Events
The Events tab houses a table that shows all endpoint events and offers filtering capabilities. Filter by Unread, Read, Unresolved Events, Quarantined, Overridden, and Blocked.
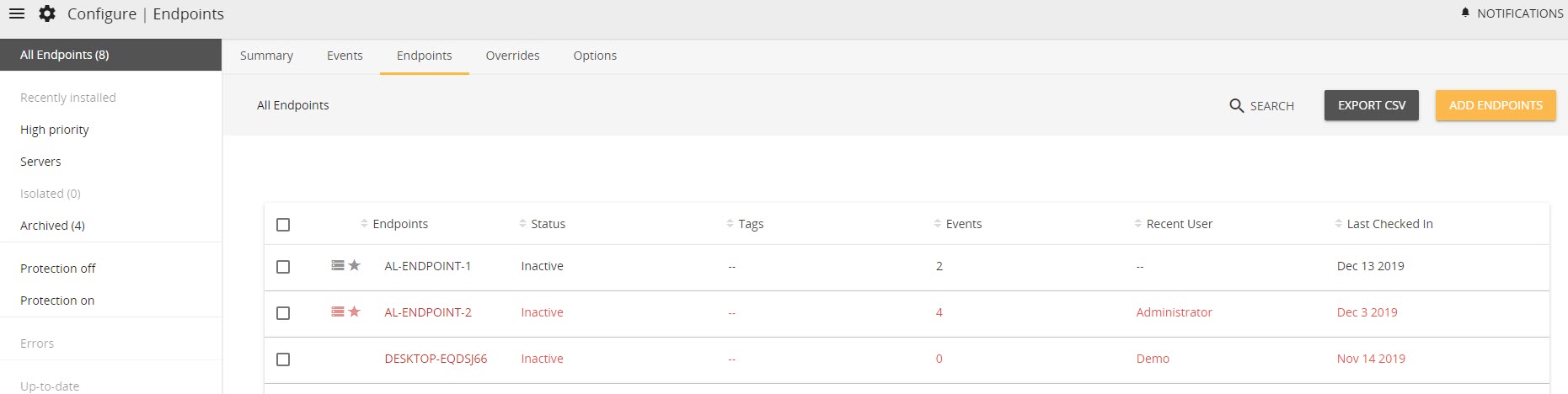
Endpoints
The Endpoints tab houses a table that shows all endpoints, offers extensive filtering capabilities, and allows for CSV export and the addition of endpoints to the environment.
Overrides
The Overrides tab houses a table that shows all overridden events that an administrator in your organization marked as trusted. Programs on this list will not trigger events.
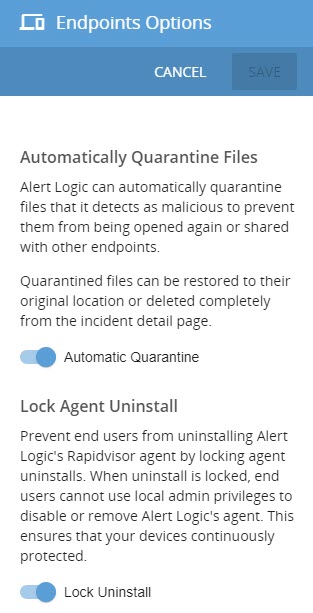
Options
The Options tab opens a side panel that allows you to turn on and off Automatic Quarantine and Lock Agent Uninstall.
PCI Scanning
The PCI Scanning page houses a list of scans and the ability to manage and schedule those scans, as well as details on your environment's PCI compliance.
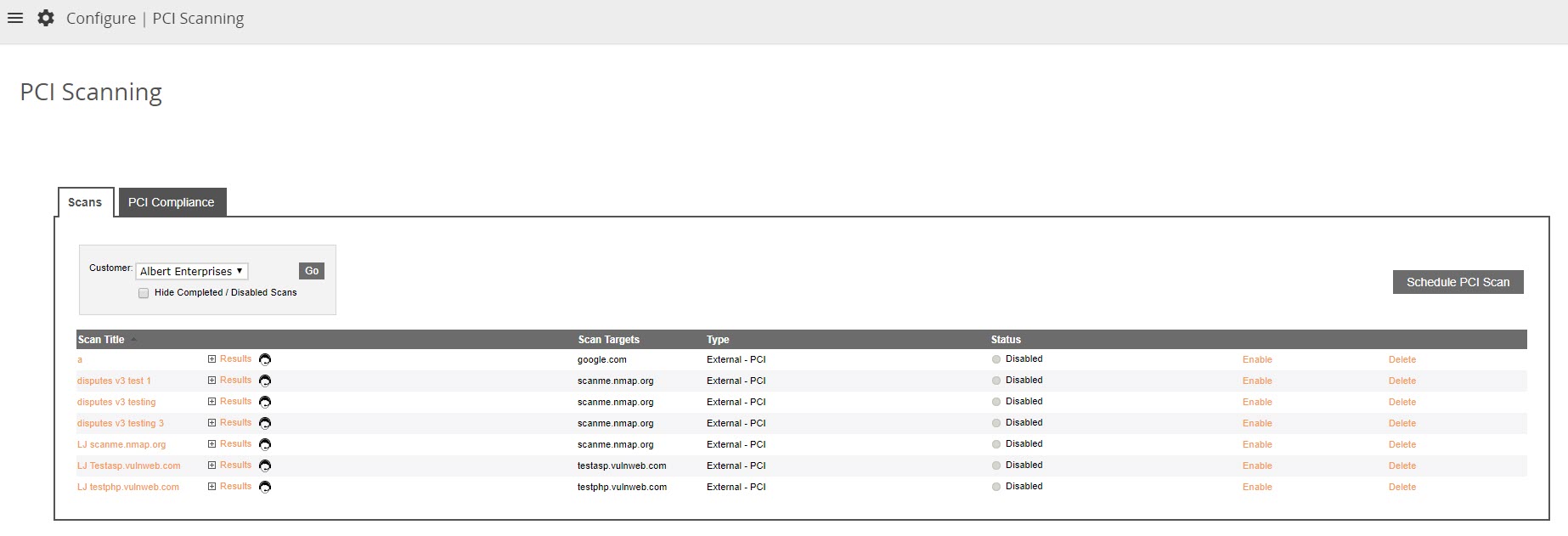
Scans
The Scans tab houses a table that shows details about your account's PCI scans, including result, scan targets, type, and status. Toggle between accounts if you manage more than one with the Customer drop-down menu in the top left corner. Within the table, you can enable/disable or delete an existing PCI scan and schedule a new PCI scan by clicking Schedule PCI Scan.
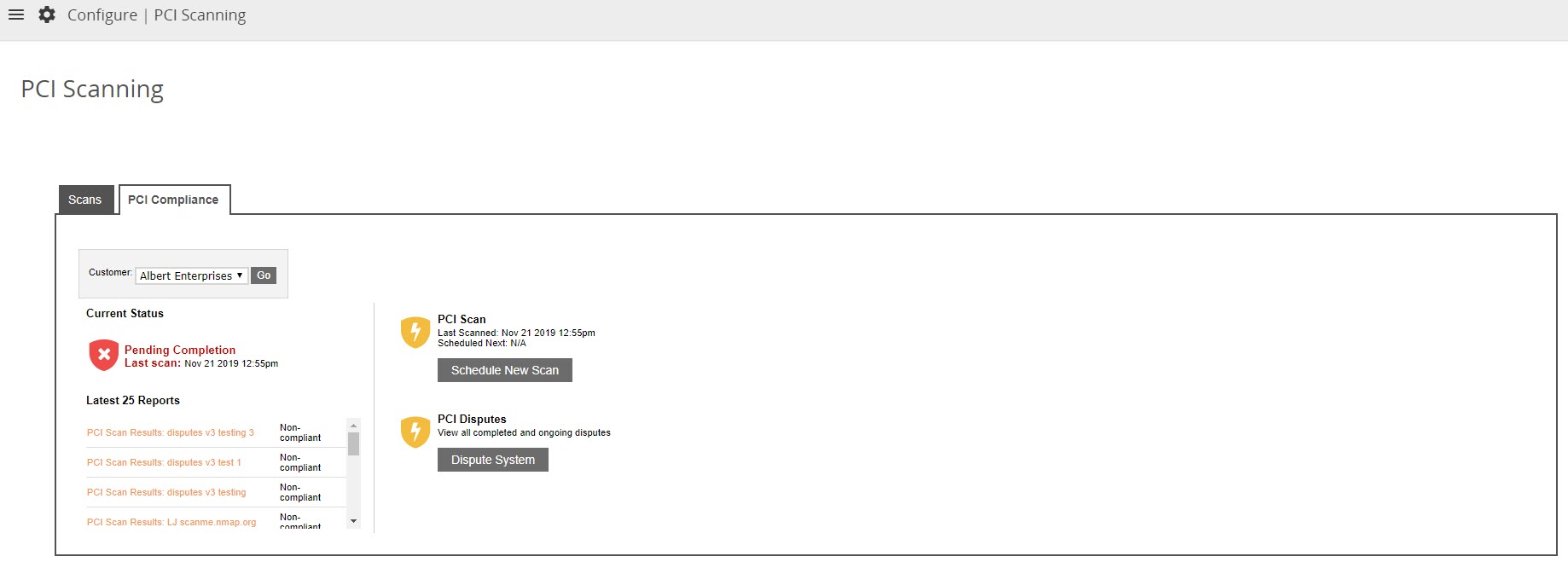
PCI Compliance
The PCI Compliance tab shows the current status of your PCI compliance and your 25 latest PCI reports. Dispute a failed report or re-scan by clicking into a non-compliant scan from the Latest 25 Reports list. Schedule a new scan and dispute a scan here, as well.
Learn more about PCI scanning with our PCI scanning best practices documentation.
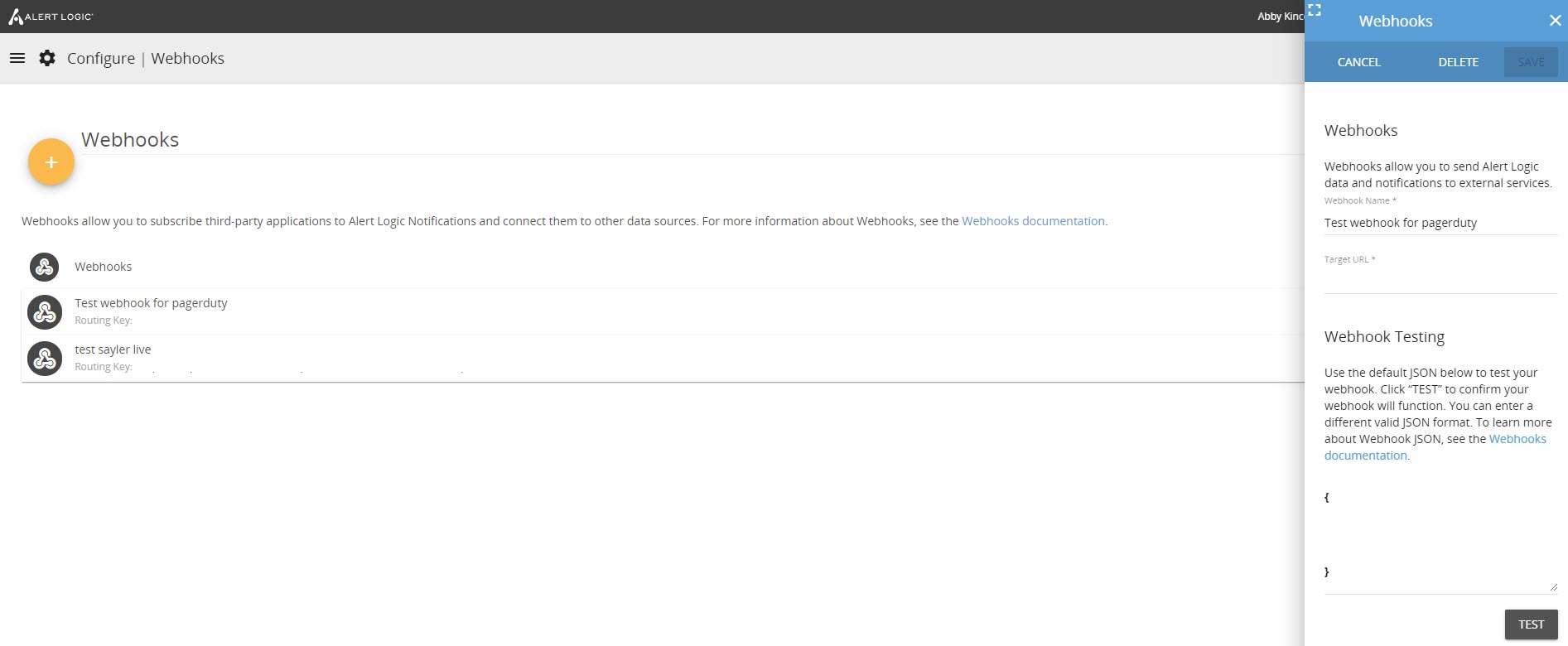
Webhooks
The Webhooks page allows you to manage - add, edit, delete, or test - webhooks.
Learn more about webhooks with our Webhooks documentation.
Comments
0 comments
Please sign in to leave a comment.